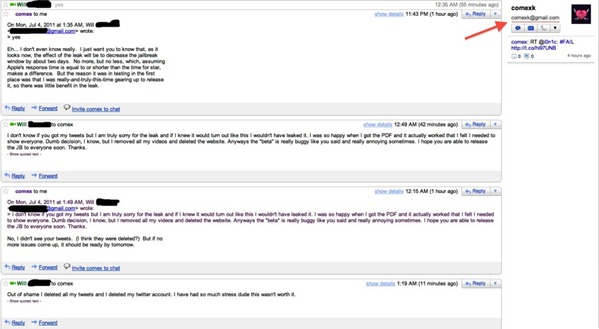
If you’ve been paying attention to the tech news over the weekend, you’re probably aware that the first untethered jailbreak for the iPad 2, dubbed JailbreakMe 3.0, was leaked to the public. While at first we speculated that one of the testers had leaked it, it turned out that it was spotted by accident, before it was sent to tech sites all over the Internet. In an e-mail exchange between the leaker and Comex himself, the official version of JailbreakMe will be released either today or tomorrow.
A MacRumors forum member named MultiMediaWill, who was responsible for making the release public, has then tried to apologize to Comex via email, after deleting all the files "out of shame". In the exchange, Comex pointed out that an early leak could cause damage, since Apple would now have the tools to fix the vulnerability before the official tool is even released. While that might be true, the early leak has also pushed Comex to release the jailbreak earlier: later today or tomorrow, according to his e-mail:
if no more issues come up, it should be ready by tomorrow
There’s some speculation around what Comex meant by "tomorrow", since his email was sent at 12:15 AM. It’s possible that Comex actually meant "today". If so, expect JailbreakMe 3.0 to be available any moment now.
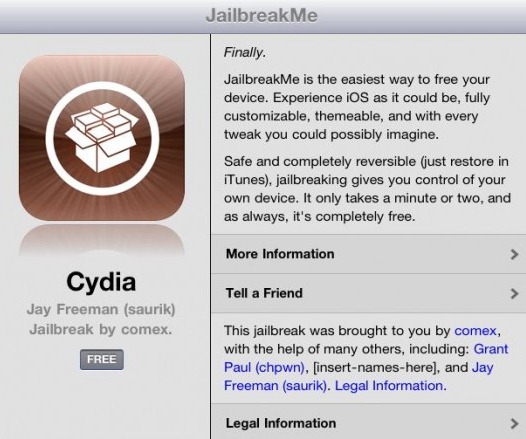
JailbreakMe is such a threat to Apple mainly because of its simplicity and effectiveness. Released way back in 2007, and updated to support new devices and operating systems ever since, this hack can be applied by simply pointing Safari to jailbreakme.com and tapping on a link to begin the process. A few minutes later, the iPad, iPod touch or iPhone will be jailbroken and Cydia will be installed. Unlike other methods, which offer mostly tethered jailbreaks on newer devices, JailbreakMe is fully untethered and can be applied in a fraction of the time.
A few days ago, we speculated that Apple could be readying a final iOS 4 release, dubbed 4.3.4, in order to fix the vulnerability used by JailbreakMe 3.0: a PDF exploit in Mobile Safari, which can be exploited by anyone with malicious intent to essentially take over the phone. Users are encouraged to backup their 4.3.3 blobs using an appropriate tool and stay away from 4.3.4 if it does come out.
Check out the whole exchange here.
(Thanks Andrea! via iPhoneItalia)
You can follow us on Twitter or join our Facebook fanpage to keep yourself updated on all the latest from Microsoft, Google and Apple.

