It is becoming increasingly rare for few days to pass by without us hearing about yet another malicious Android app that is loaded with ransomware, and sent out into the wild to wreak havoc amongst unsuspecting users. Just a few days back we heard about a ransomware which communicated over XMPP, and now a new strain, being dubbed Android/Lockerpin.A, appears to be taking things to a higher, more sophisticated level, by setting or resetting the PIN that is required to grant access to the Android device. Device owners are then forced to perform a factory reset and wipe all data from the device, or shell out $500 to the malicious individuals operating the malware, which is the really the standard course of action now.
Like most malicious installations that are embedded with digital evil, this latest creation first of all requires the device owner to grant it administration privileges so that it can’t enact its devious intent. In order to trick users into providing full system access, Android/Lockerpin.A “overlays a bogus patch installation on top of an activation notice”. By clicking on the relatively innocent “Continue” button, users are inadvertently providing permission to the app to make a series of changes to the Android system. Thus preventing user access to the device by setting an unknown PIN code.

One of the things that makes this particular strain of ransomware more devious is that it doesn’t seem to be easily defeated. Earlier strains of ransomware embedded within malicious apps could be combatted by booting the device into Safe Mode and removing administrate privileges. More so, according to analysts, this particular exploit works to defend itself from installed AV apps as well by pushing bogus windows with the ‘Continue’ button if and when detected. Due to the nature of Android/Lockerpin.A, and the fact that it changes the PIN code at system level, it seems that a factory wipe is the only real solution to the lockdown, unless you have a rooted phone, and some experience with ADB:
After clicking on the button, the user’s device is doomed: the Trojan app has obtained Administrator rights silently and now can lock device — and even worse, it set a new PIN for the lock screen.
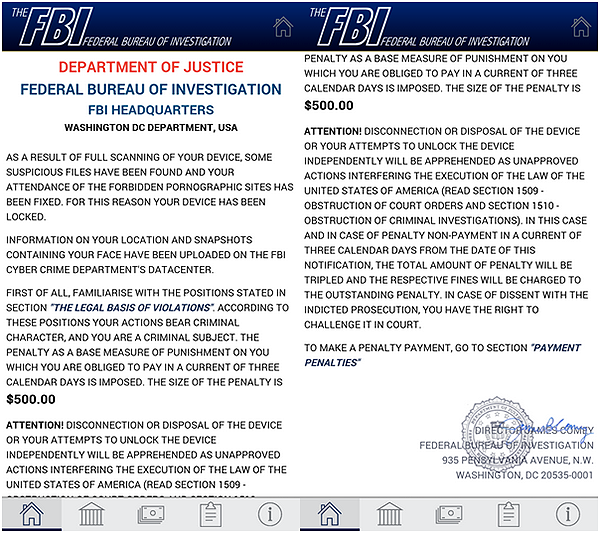
A short while later, the user will be prompted to pay $500 for allegedly accessing illegal obscene websites and for storing such content on their phone as well.
The ransomware isn’t really classified as providing a large-scale threat to Android owners just yet. It’s currently offloaded onto devices via third-party Android app stores via an application that promises to serve up p*rnography to those downloading it. That in itself should be enough to set alarm bells ringing and keep users away. However, the potential exists for this to infect the mainstream Google Play, giving it access to millions of more devices.
(Source: WeLiveSecurity)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

