With this year’s Hack in the Box (HITB) conference in Singapore on the horizon, security is most definitely the topic of conversation in the smartphone world. As many panelists and speakers prepare their content and sessions for that conference, security researcher and hacker xerub has been hacking around with Apple’s Secure Enclave Processor (SEP) for Touch ID, resulting in the “fully grown” decryption key for iPhone 5s being posted online.
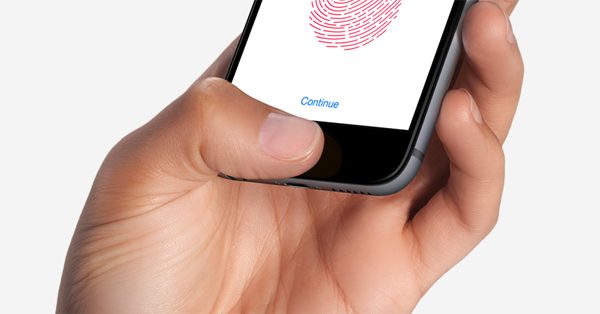
The posting of the decryption keys online will instantly set alarm bells ringing internally within Apple. Apple hardware fans may remember that Apple made quite a big deal about the security coprocessor and its secure enclave when the iPhone 5s was introduced alongside the wonderful Touch ID functionality.

The job of that particular section of the hardware is to function as its own entity and provide secure work on behalf of the main SoC within the device. In addition to that work, the SEP also prevents the main processor from accessing secure sensitive data, essentially segregating the two sections. The release of the iPhone 5s decryption key for SEP means that anyone with the relevant experience and expertise in this particular field can use the img4lib library to decrypt the firmware (SEPOS) which powers the secure enclave processor inside iPhone 5s. This firmware includes its own kernel, drivers, and services which power the whole experience.
The hacker involved has also released his SEP firmware split tool to process. But let’s be clear on this, the release of the decryption key for iPhone 5s doesn’t mean that Apple’s secure enclave has been violated or hacked and that all sensitive or secure data is now accessible to malicious individuals. It does mean that the availability of the decryption keys will allow security researchers, hackers, and potentially individuals with malicious intent, to investigate the firmware on a granular level on iPhone 5s to try and detect any vulnerabilities which could be exploited to gain access to the information contained within.
At the time of writing, there is no information to suggest that anyone has actually taken advantage of the situation yet and gained access to the system, but nevertheless, it will be a cause for concern for Apple even though it only appears to effect iPhone 5s.
You can see the original post and find more information about img4lib and SEP firmware split tool over at xerub’s Twitter account.
Update: As pointed out by Will Strafach, Secure Enclave has not been hacked. “Decryption key in this case is for the firmware, allowing more researchers to look at it.” The post above has been updated to reflect this change.
You may also like to check out:
- Download LibreELEC Kodi 17.4 Krypton 8.1.0 Beta
- Game Of Thrones S07E06 Download Leaks Online By HBO Spain
- Cydia Remover For iOS 10 Is A Cydia Eraser Alternative For Latest Firmware Versions
- Download iOS 11 Beta 6 & Install On iPhone 7, 7 Plus, 6s, 6, SE, 5s, iPad, iPod [Tutorial]
- Jailbreak iOS 10.3.3 / 10.3.2 / 10.3.1 / 10.3 For iPhone And iPad [Latest Status Update]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

