On occasion, it can be marketing gold for a product or service offering to be known as “the first” to achieve a specific milestone or do a certain something. Unfortunately for Transmission, which is one of the most commonly used BitTorrent clients on the OS X platform, becoming the first Mac application to be infected with ransomware is probably not something that’s going to help with user confidence, and it’s certainly not something that’s going to drive growth and force more users to download and trust the Transmission experience on their Macs.
The Transmission app and platform has millions of active users who have not only utilized the services of the app for quite some time, but have also had no prior reason to distrust or shy away from using it. It’s quite popular, and for the most part has become one of the immediate app installations for those who require a functional, feature-rich BitTorrent client on Macs. However, it has been noted that the app has now become a hosting ground for a particular type of ransomware that can potentially encrypt the computer.

The developers of the ransomware then demand that the user parts with an online Bitcoin payment of around $400 in order to have the machine decrypted. The detected malware first became public knowledge when a set of users took to the Transmission forum to report its existence. It was quickly identified as “OSX.KeRanger.A”, with several people posting in the forums managing to drill down and investigating enough to determine that it’s likely associated with the version 2.90 of Transmission.
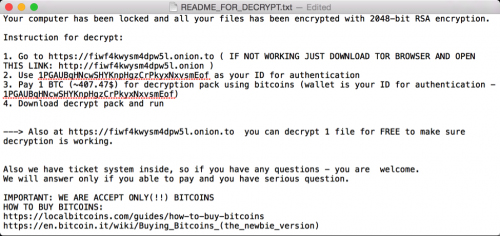
Those suspicions, albeit largely already confirmed, were then backed up and officially “confirmed” after some investigation by a security analytics firm, who also took the opportunity to publish a full warning and overview of the ransomware:
On March 4, we detected that the Transmission BitTorrent installer for OS X was infected with ransomware, just a few hours after installers were initially posted. We have named this Ransomware “KeRanger.” Attackers infected two installers of Transmission version 2.90 with KeRanger on the morning of March 4.
The security analytics firm has conducted a full technical analysis of the KeRanger malware which has confirmed that the malware has been signed with a valid Mac app development certificate, a process that allows it to pass seamlessly through Apple’s Gatekeeper protection built into OS X. They have also provided users with additional information on how to protect themselves and the action to take if they believe they may have already been affected by a KeRanger install.
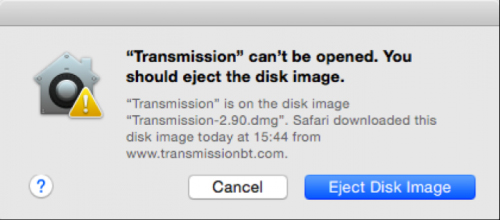
Apple is aware of the issue and as such has already updated its XProtect signatures, revoking the abused certificate. Because of this, if an infected version of Transmission is now opened, a warning will be shown as shown in the screenshot above. Eject the disk image when prompted and delete the installer completely afterwards.
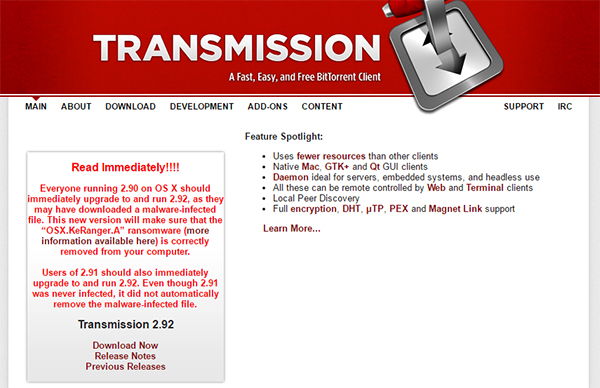
Transmission has also reacted to this dangerous development by releasing version 2.92 of Transmission for Mac, and has advised all users running version 2.90 and 2.91 to update as soon as possible. Version 2.91 may not be infected, but it does not automatically remove the infected files that came with version 2.90. Updating to version 2.92 is hence important as it not only comes free of the malware, but also helps in removing the malware from the already-infected systems.
(Source: Palo Alto Networks)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

