Discover effective strategies to safeguard your digital assets from ransomware attacks. Follow these essential tips to enhance your cybersecurity and protect against potential threats.
Here are the 5 best AI cover letter generators compared for 2024 for your guidance.
With the forecast of 15.14 billion internet-enables devices by the end of 2023, notoriously poor IoT security raises concerns for businesses and users alike. What can we learn from IoT hacks?
Here is how you can remove TikTok watermarks with these 9 useful tools, complete with guide on how to use them.
YouTube's Susan Wojcicki is stepping down from her role as CEO. Here's everything you need to know about this.
Microsoft has announced a new ChatGPT-Powered Bing search and Edge browser, Here’s how you can try it right now.
Apple's revamped iCloud.com website with an all-new design has launched. Here are all the details on this.
Here's how to remove background from images using PicWish, complete with instructions.
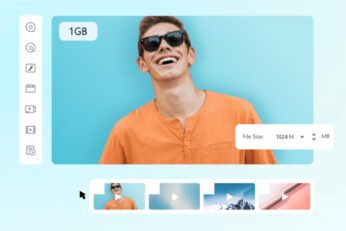
Here's how to help reduce video size, both online and offline, the right and easy way.
Netflix has just announced a new 'Basic with Ads' tier at $6.99 per month. Here are all the details on this.