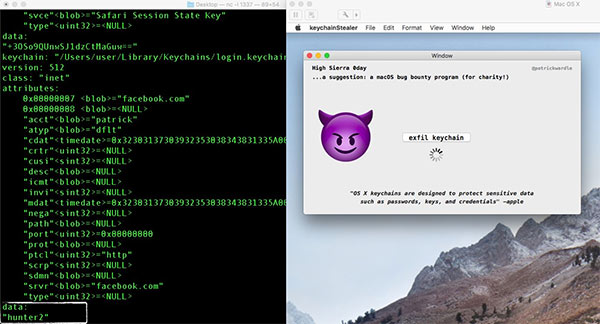
A new macOS vulnerability which allows apps to access passwords in plain text and should normally be protected by Apple’s Keychain system has just been discovered and demoed.
The discovery was made by security researcher Patrick Wardle and impacts multiple versions of Apple’s macOS operating system, including the High Sierra release which arrived yesterday. Apple is aware, and will likely be issuing a fix in the form of software update soon.

Normally, credentials held in Keychain are protected by 256-bit AES encryption, making it almost impossible to crack. The theory goes that only apps which are authorized to access the data can do so, but Wardle has shared a video in which an app, created by him, is able to access credentials for Facebook, Twitter, and even Bank of America.
Wardle, being a responsible researcher, told Apple of the security hole on September 7th and has not disclosed the method he used, but the fact that this works for both signed and un-signed apps will be a worry for Apple, as if it was not already concerned about the potential for apps to dive deep into Keychain and extract data that could give naughty people the ability to gain control of all kinds of accounts owned by Mac users.
Importantly, Wardle does not suggest people use this as a reason not to update to High Sierra, given the fact that it impacts older versions of macOS (OS X), too.
I think everyone should update. There’s a lot of good built-in security features. This attack works on older versions of macOS as well. There’s no reason for people not to upgrade.
Apple’s High Sierra can be downloaded for free from the Mac App Store right now, having been made available for the first time yesterday.
(Source: @patrickwardle [Twitter])
You may also like to check out:
- Download iOS 11.0.1 IPSW Links For iPhone, iPad, iPod touch
- How To Downgrade iOS 11.0.1 / 11 To iOS 10.3.3 / iOS 10 [Tutorial]
- Download iOS 11, 11.0.1 Links & Install On iPhone 8, 7 Plus, 6s, 6, SE, 5s, iPad, iPod [Tutorial]
- Jailbreak iOS 11 / 11.0.1 On iPhone And iPad [Status Update]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

