There has been quite the noise online over the past 24 hours after it was announced that all of Intel’s modern CPUs come with a security flaw that could potentially have devastating consequences. While Apple hasn’t shed any light on it publicly yet, but it appears that fixing it on a Mac involves isolating the kernel’s memory from user processes via Kernel Page Table Isolation.
This works at the operating system level and was expected to come with a performance hit. While all computers with Intel chips are impacted, regardless of operating system used, it would appear that Apple has already partially issued a fix for Macs.

According to developer Alex Ionescu, Apple introduced a fix in macOS 10.13.2, with additional tweaks set to be introduced in macOS 10.13.3 – a release that is currently in the hands of developers via the beta testing channels. AppleInsider also cites “multiple sources within Apple” when claiming that changes made in macOS 10.13.2 mitigated the majority of security concerns that are associated with the vulnerability.
The design flaw, part of Intel chips across the board, allows applications to see some of the contents of what should be protected kernel memory. This could theoretically give attackers the opportunity to extract passwords or other data when it should not normally be readable by anything other than the system itself. The fix, isolating the kernal’s memory, could slow computers down by anything from 5% to 30% according to estimates, but it would appear the Mac may not be so heavily impacted in this regard. If macOS 10.13.2 does indeed include a fix, we have yet to hear of any performance issues as a result of the update.
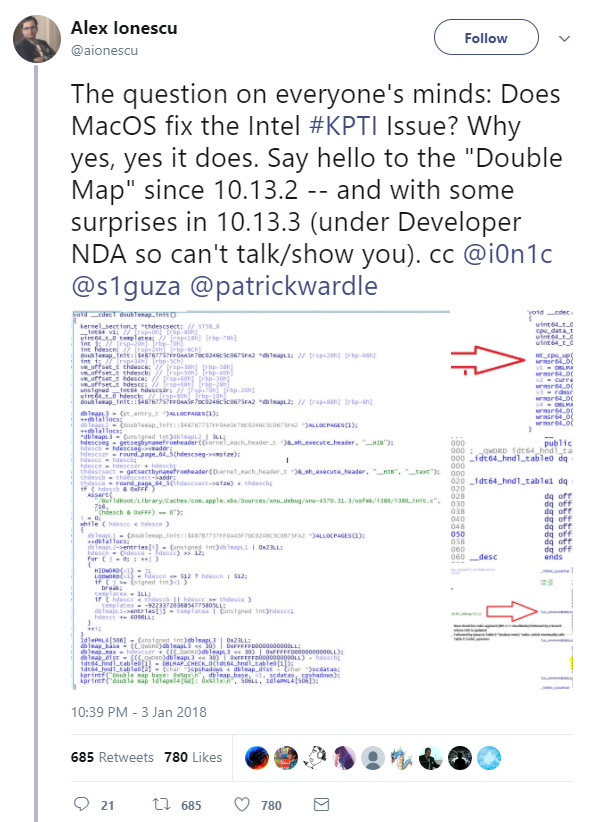
Ionescu believes that any performance drop on a system using PCID (Process-Context Identifiers), available on most modern Macs, is likely to be “minimal.” With that in mind, it’s likely most normal Mac users would not experience any noticeable change in performance during their general usage.
(Sources: Alex Ionescu [Twitter], AppleInsider)
You may also like to check out:
- iOS 11.2.5 Beta 3 Changes, Release Notes And Changelog Details You Need To Know About
- iOS 11 / 11.1.2 Jailbreak Now Allows Some Cydia Tweaks To Be Installed Thanks To New To.Panga Update
- iOS 11.2.5 Beta 3 IPSW / OTA Download Released, Here Are The Details
- Houdini Beta 2 IPA iOS 11 / 11.1.2 Semi-Jailbreak Released [Download]
- Jailbreak iOS 11 / 11.1.2 Using LiberiOS, Here’s How [Tutorial]
- Jailbreak iOS 11.2.1 / 11.2 / 11.2.5 On iPhone And iPad [Status Update]
- Downgrade iOS 11 / 11.2.1 To 11.1.2 On iPhone Or iPad [How-To Guide]
- Jailbreak iOS 11 / 11.1.2 On iPhone X, 8, 7, iPad Using LiberiOS [Updated]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

