If you’ve been trying to figure out a way to jailbreak your iPhone 4 or 3GS running iOS 4.3.3 and none of the existing methods seem to be working for you, try JailbreakMe 3.0. This new method allows you to jailbreak your device by simply navigating over to a webpage.
Sounds too good to be true, right? Wrong, it’s actually very real. By taking advantage of a PDF exploit in Mobile Safari, it can execute code straight from your phone, jailbreak it and install Cydia.
Here’s how you do it:
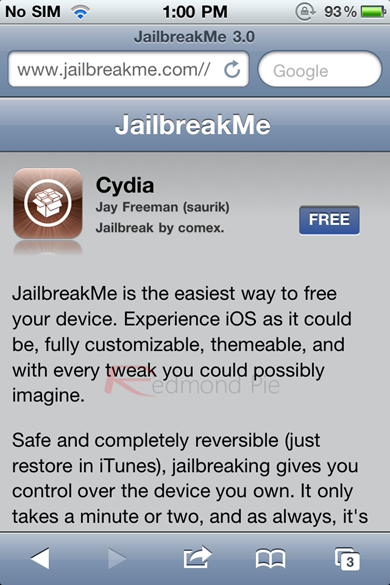
Step 1: Point Safari to http://jailbreakme.com/. The following screen should show up:
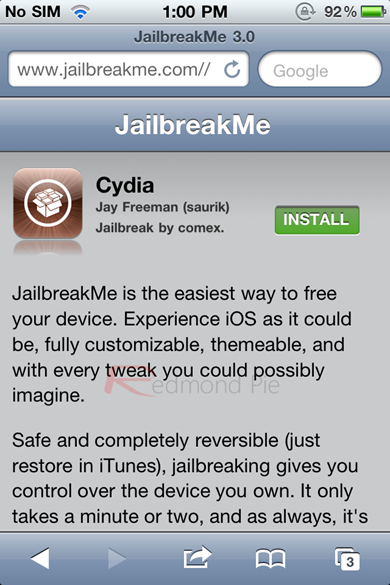
Step 2: As the website instructs, tap on “FREE” button, followed by “INSTALL” to begin the jailbreaking process.
Step 3: No further interaction is needed from here on. JailbreakMe will take advantage of the PDF exploit to take over your device and load Cydia onto it. A progress bar on Cydia’s icon, on home screen should indicate the progress: as long as it’s moving, don’t interact with it, it will do its job on its own.
Step 4: Once the process is finished, you should have Cydia installed on your device. It’s that simple!

If you’ve never jailbroken your device, this can be a really great way to get started. Unlike other methods, this doesn’t require a computer connection and is untethered, meaning that unlike other methods such as Redsn0w, you don’t need to hook up your device to your computer every time you boot it up in order to boot it into a jailbroken state.
This method first surfaced in 2007 when a PDF exploit in Mobile Safari was first discovered. That first exploit was fixed soon after, but others popped up, causing this method to live on until today, with JailbreakMe 3.0. If you’ve applied a jailbreak using this method in the past, you should feel right at home, since the process is exactly the same.
There are rumors that a new version of iOS 4, iOS 4.3.4, will come out soon to fix this serious PDF Exploit, even as Apple is hard at work developing iOS 5. If you’re planning on using this method, make sure you don’t update to 4.3.4 is it ever comes out. Meanwhile, enjoy this vulnerability while it lasts.
You can follow us on Twitter or join our Facebook fanpage to keep yourself updated on all the latest from Microsoft, Google and Apple.

