There are several ways to jailbreak iOS devices, but most of them are time-consuming as they require you to connect your device to your computer for the jailbreak to complete. Thankfully, JailbreakMe 3.0, just like previous versions, allows easy jailbreaks by simply visiting the JailbreakMe.com website, thanks to a PDF exploit in Safari.
This method truly is the simplest way to jailbreak your device on iOS 4.3.3, and it’s fully untethered, meaning that you don’t have to plug your device into your computer in order to boot it into a jailbroken state. Adding to JailbeakMe’s advantages is its compatibility, since it works with every device on the face of the earth (running firmware 4.3.3), including the iPhone 4 and the iPad 2 (3G, CDMA & WiFi models). Support for iOS 4.3.1, 4.3.2 and 4.2.1 will be added later. iOS 5 betas are not supported.
Without further ado, here’s how easy it is to apply this jailbreak:
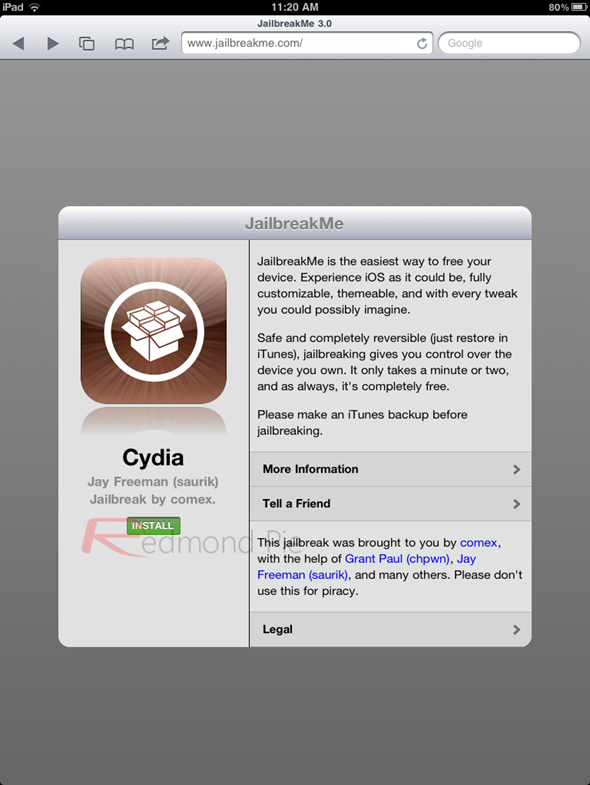
Step 1: Launch Safari and point it to http://jailbreakme.com. If everything goes as expected, you should see this on your browser:
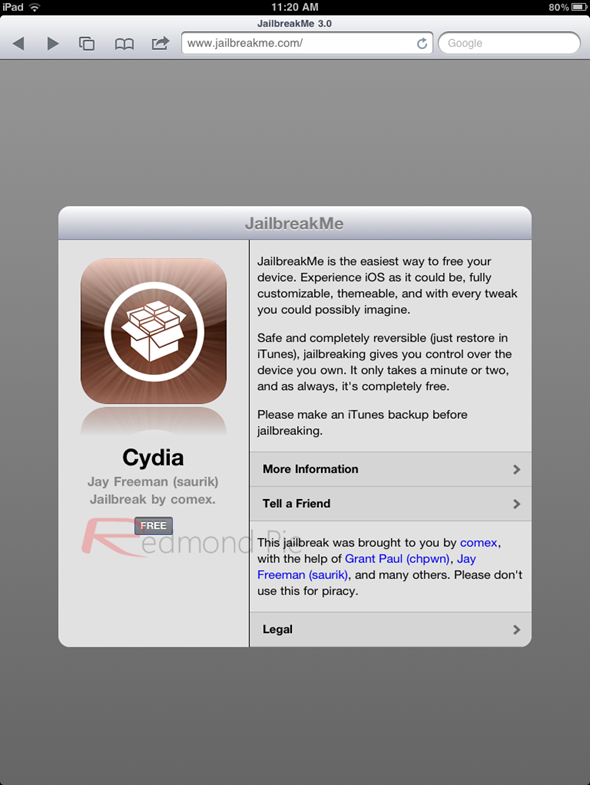
Step 2: As instructed, tap on the “FREE” button, followed by “INSTALL”. Only do this once, even if you get stuck here for a few seconds.
Step 3: You’re essentially done here. The hack will now take advantage of an exploit in your browser to load the necessary files onto your system and execute a jailbreak script right on your handset. Safari should automatically close, you should now see a Cydia icon on your Home Screen, with a progress bar, much like any other official app while it’s downloading.

Step 4: Once that’s done, you should now see Cydia on your iPad 2’s Home Screen!
If you’re new to the jailbreaking world, this can be a perfect way to get started. This method first surfaced in the fall of 2007 as an effective jailbreak for iOS 1.1.1 (those were the days). It relied on a PDF exploit, just like the version that was released today (although, of course, a different exploit). If you’ve ever jailbroken any iOS device using a previous version of JailbreakMe, you’ll be able to do it just as easily using version 3.0, since the method is exactly the same.
Despite its simplicity, it’s important to stress that this method enables a fully-featured untethered jailbreak, there are no caveats. And since everything is done on the OS side, there’s no limit on what kind of hardware it can support, at least until the specific PDF exploit this relies on gets patched (which it likely will pretty quickly, possibly with iOS 5 Beta 3 or iOS 4.3.4). If you’re planning to stick with iOS 4, however, you should be pretty safe for a while.
You can follow us on Twitter or join our Facebook fanpage to keep yourself updated on all the latest from Microsoft, Google and Apple.

