The maker of the iPhone, iPad and Apple TV has updated its iOS Security document to include intricate, detailed information pertaining to the Touch ID sensor that is found on the iPhone 5s. The launch of the iPhone 5s, along with the ability to authenticate and access the device using biometric detection, brought with it a myriad of questions and concerns from the security conscious. Apple hopes that the updated PDF document will answer a few of those outstanding concerns.
The information that has been added to the existing security document is predominantly focused on how the Touch ID sensor works, as well as providing additional information about the accompanying Secure Enclave that stores and keeps the user’s data private. The detailed information provided in the document may fly straight over the head of the average iPhone user, but for all others it is a truly interesting eye opener that should encourage users to have a lot more faith in the security abilities of the system.

Each A7 processor that sits within the shipped iPhone 5s comes with its own Secure Enclave that is responsible for handling and authenticating the fingerprint data that is captured and passed on by the user-facing Touch ID hardware. At the time of manufacture, each Enclave is assigned an entirely unique identifier that is kept entirely separate from the rest of the iOS ecosystem and therefore cannot be accessed by anything else. The provisioned identifier isn’t even known to Apple. The identifier is then used as part of the start-up process to generate an additional key that is used to “encrypt the Secure Enclave’s portion of the device’s memory space“.
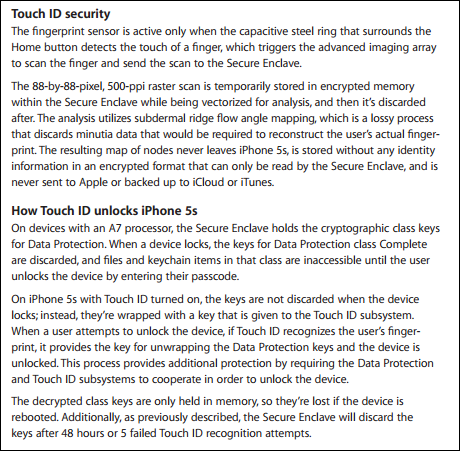
The updated security document also outlines a few additional details about how the device handles the fingerprint image that is provided to it as part of the print registration process. The Touch ID sensor captures an 88 x 88 pixel representation of the provided fingerprint, sends it to the Secure Enclave to be turned into a decryption key and then discards it without ever storing the information on Apple’s own servers or any device based backup. The document also states that the decrypted keys are discarded after 48-hours or five failed Touch ID recognition attempts, whichever comes first.

If the security of your information on the iPhone 5s is of paramount concern, or if you just want to read Apple’s updated document then check out the PDF here.
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

