If you have been following along with how Epic Games is getting Fortnite into the hands of Android gamers, then you will already know that it isn’t publishing it via the Google Play Store like normal but is instead using its own delivery mechanism.
It’s a process that means it will not have to hand over a portion of the game’s takings, but it also comes with its own problems. As Google has now confirmed, a vulnerability in the Fortnite for Android installer allowed any app on a phone to then download and install anything it wanted, all in the background, without the user’s knowledge. That’s pretty grim reading.

Google apparently noticed the issue and told Epic Games about it back on August 15th, with Epic having now patched its software to prevent the issue from continuing. Google is sharing the information publicly now, reminding us all of just how difficult it is to do things on Android without accidentally opening the floodgates for all manner of nastiness. Especially if you try to bypass Google’s own store.
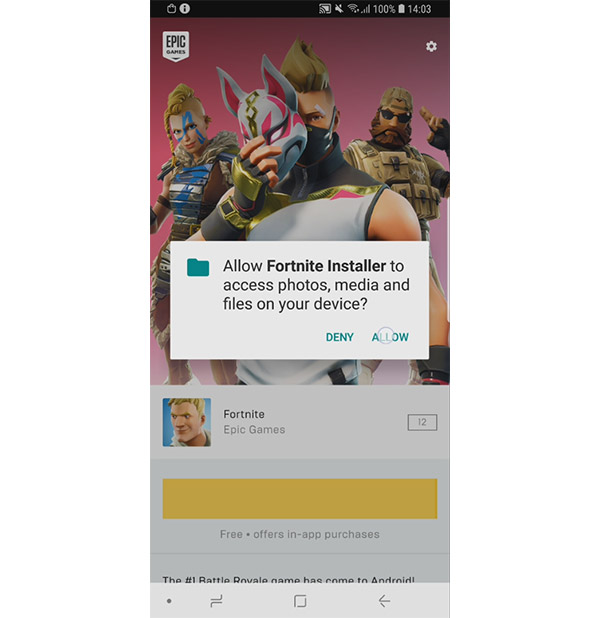
The process of installing Fortnite on Android currently involves downloading an installer, an app that then goes off and downloads the rest of the game directly from Epic. The issue, according to Google, was that the installer itself was easily exploited, opening the possibility to it hijacking the request to download the additional data and replacing it with one to download, well, anything.
Despite Google potentially saving it from a world of hurt, Epic Games couldn’t bring itself to be too grateful.
Epic genuinely appreciated Google’s effort to perform an in-depth security audit of Fortnite immediately following our release on Android, and share the results with Epic so we could speedily issue an update to fix the flaw they discovered.
However, it was irresponsible of Google to publicly disclose the technical details of the flaw so quickly, while many installations had not yet been updated and were still vulnerable.
An Epic security engineer, at my urging, requested Google delay public disclosure for the typical 90 days to allow time for the update to be more widely installed. Google refused. You can read it all at https://issuetracker.google.com/issues/112630336
Google’s security analysis efforts are appreciated and benefit the Android platform, however a company as powerful as Google should practice more responsible disclosure timing than this, and not endanger users in the course of its counter-PR efforts against Epic’s distribution of Fortnite outside of Google Play.
The good news here is that for this issue to really become a huge one, users would need to have an app installed that was capable of taking advantage of the installer flaw, something that is very unlikely as of right now, but the fact this was even possible in the first place should be a warning to any other developer contemplating going around the Play Store.
You may also like to check out:
- Download iOS 12 Beta 10 IPSW, Public Beta 8 OTA Update
- Jailbreak iOS 11.4.1 / 11.3.1: iOS 12 Beta 9 SEP Is Compatible With Electra Jailbreak Supported Firmware
- Download: Android 9 Pie Factory Images, OTA For Pixel, Essential Phone Released
- Download iOS 11.4.1 Final IPSW Links, OTA Update For iPhone And iPad
- Download iOS 12 Beta 10 Configuration Profile File Without Developer Account
- Download iOS 12 Beta 10 IPSW Links & Install On iPhone X, 8, 7, Plus, 6s, 6, SE, 5s, iPad, iPod [Tutorial]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

