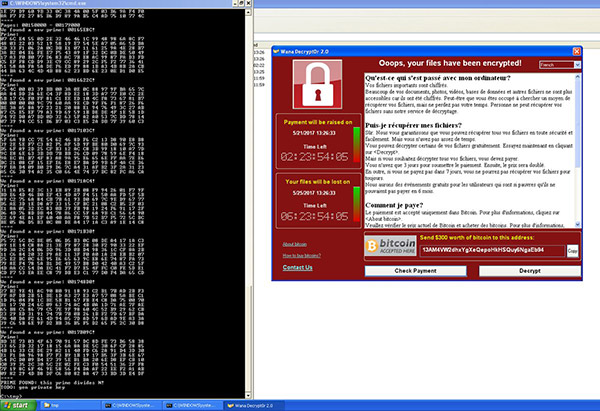
Ransomeware is bad – very bad, and that is very much the case with the WannaCry ransomware that has taken the world by storm over the past week, with huge companies and health organizations suffering at the hands of the ransomeware that demands $300 per machine to decrypt its data.
However, one security researcher may have found a way to strike back, at least in part, while retrieving data and avoiding that $300 fee.

Now, before we get anyone’s hopes up, this workaround as such will only apply to a very limited number of scenarios. For starters, it only works on computers that are using Windows XP as their operating system, and even then, only when they have not been restarted since the infection took hold.
Even if those criteria are met, you may still be out of luck. That’s because the tool released by the researcher, called Wannakey, takes the encryption key right out of the memory of an affected system, meaning this is only going to work in a very specific, very small number of cases. If you fit into that category though, you won’t care about that one jot!
Wannakey has been developed by Adrien Guinet, a researcher for French outfit Quarkslab, and posted on GitHub for free to allow as many people to take advantage of it as possible. From the “README” file on the Wannakey GitHub page:
This software has only been tested and known to work under Windows XP. In order to work, your computer must not have been rebooted after being infected.
Please also note that you need some luck for this to work (see below), and so it might not work in every cases!
While the chances of this helping you if you are infected with WCry are small, even if it helps one person, it is well worth the time and effort to distribute. Good luck, folks! It’s a dangerous world out there.
(Source: aguinet [GitHub], Bottom image: Adrien Guinet [Twitter])
You might also like to check out:
- Enable Hidden Touch-Optimized File Explorer In Windows 10 Creators Update, Here’s How
- iOS 10.3.1 Jailbreak Promised By A Security Researcher But It Might Take A While
- Install Android 8.0 O Beta OTA Update On Pixel And Nexus Devices, Here’s How
- Download: Android 8.0 O Beta 1 Now Available, Here Are The Details
- iOS 10.3.3 Beta 1 Release Notes, Changes And New Features
- Jailbreak iOS 10.3.2 / 10.3.1 / 10.3 / 10.2.1 For iPhone And iPad [Latest Status Update]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

