Couple of Apple Activation Lock bypass have been discovered, with iOS 10.1.1 – the latest public version of the firmware – also being vulnerable to one of them.
First, let us explain what Activation Lock is on iOS devices. Introduced first with iOS 7, Apple’s Activation Lock is a really handy feature that lets users lock their iPhone or iPad from a remote location if it has been lost, stolen or just temporarily misplaced with fear that it may be in malicious hands.

It’s designed as a way of protecting a device, but as mention earlier, security researchers have found a way to bypass that feature using a previously unknown bug in Apple’s ecosystem.
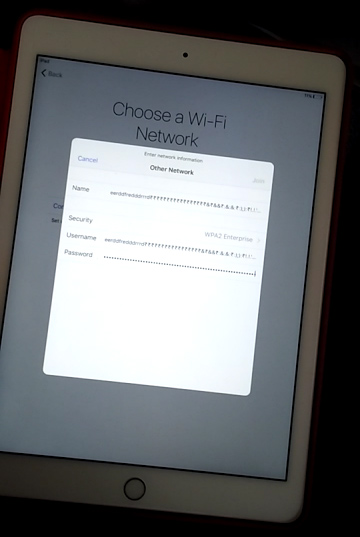
Security researcher Hemanth Joseph became the first person to knowingly come up with a solution to bypass Apple’s Activation Lock feature after purchasing a second-hand iPad from eBay. It’s unknown if the attempt was deliberate or not, but it seems that Joseph was able to crash the entire security software layer on the locked device running iOS 10.1 by entering a ridiculously long string of characters into the iPad as a password for the Wi-Fi setup process.
When a Activation Locked device is powered on, as part of the usual process, the system allows a user to select a WiFi network and then input the correct credentials to gain access to the Internet. User is then asked to provide the correct Apple ID credentials with which the device is locked so that it can be cross-referenced remotely with Apple’s servers for disabling Activation Lock and regaining full access to the device.
However, in this instance, Joseph was able to trick the system by selecting “Other Network” from the list, and then entering excessively long strings of text into the “Name”, “Username” and “Password” fields. This created an unexpected overflow error. This overflow error alone isn’t enough to bypass the Activation Lock, but by using the Smart Cover to turn the screen on and off during the overflow error, Joseph was able to crash the security layer completely and gain access to the device’s Home screen. This bypass was discovered in iOS 10.1 back in November with Apple allegedly fixing the issue with the release of iOS 10.1.1.
The second discovery is even more dangerous, as it even works on iOS 10.1.1. Vulnerability Lab has been able to recreate the above exploit on iOS 10.1.1 using screen rotation lock and Night Shift mode to gain access to Activation Locked iPhone and iPad running iOS 10.1.1.
It’s by no means a perfect solution that provides unlimited access to the device, but as has been proven now that it can still be made to work on iOS 10.1.1, Apple will now have to issue a quick emergency bug fix update to fix this vulnerability completely.
Check out the proof-of-concept video below and tell us what you think.
(Source: Hemanth Jospeh, vulnerability0lab [YouTube])
You might also like to check out:
- iOS 10.2 Beta 4: Changes And Feature Improvements
- Jailbreak iOS 10 / 10.1.1 / 10.0.2 / 10.2 For iPhone, iPad, iPod touch [Latest Status Update]
- Download iOS 10 / 10.1.1 / 10.0.2 Links & Install On iPhone 6s, 6, Plus, SE, 5s, 5c, 5, iPad, iPod [Tutorial]
- Apple’s Activation Lock Status Tool Lets You Check If An iPhone Is Stolen Or Not
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

