Web security is of paramount importance to most Web users, and every now and then, something occurs that reminds us of how the determination of a hacker can result dire consequences. In a report that does make for quite disconcerting reading, someone, using a keylogger, managed to obtain over 2 million passwords of the likes of Facebook, Gmail, Twitter, Yahoo, and LinkedIn.
Security outfit Trustwave made the discovery, with the attacker capitalizing on a keylogger based upon a variant of the Pony botnet controller — a malicious utility that recently cut hackers a break when its source code was leaked out into the wild.

The method for obtaining the passwords was incredibly simple. Having installed the keylogger on millions of machines spanning 92 countries across the world, it then simply made a record of logins and passwords as they were typed. With many of us logging in to our favorite email accounts like Gmail, as well as social hunts like Facebook and Twitter, many hundreds of thousands of passwords were stolen from users each, and although this wasn’t achieved through any of our favorite services, the folks of ADP, Facebook, LinkedIn, and Twitter have already alerted affected users and reset their passwords for them.
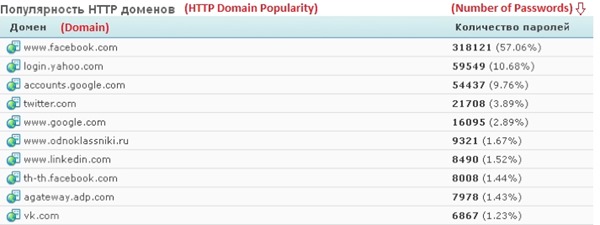
In a blog post, Trustwave listed the domains from which passwords were compromised:
For once, the response appears to have been swift and effective, and so if, in the likely event that you do use one of the aforementioned services, you’re worried, the situation seems now to be under control.
Nevertheless, Pony botnet controller managed to amass a whopping 1.5 million website logins, one-third of a million email account credentials, and a whole lot more, including the vital info on FTP and remote desktop accounts.
If you do fear for your security online, there are a series of precautionary measures you could adhere to. As well as running a reputable virus scanning / Internet security app on your machine, don’t download anything from untrusted sources.
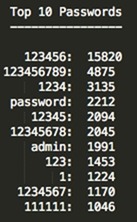
Oh, and if you’re going to create a password, make sure it’s something that cannot be easily guessed. The big companies have worked hard to prevent users from typing in simple, effortlessly compromise-able secret words, and given that Trustwave discovered that some of the most common passwords compromised here included "123456789," and "password," it’s almost as if some people want their accounts to be compromised.
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

