It is honestly beginning to feel like the Dawn of the Bugs, just that these are software bugs. The latest news to hit the Web brings to light how Skype for mobile and Windows desktop can be crashed by just about anyone using a simple eight characters based string, leaving the victim’s app in a crashing loop. But luckily, there’s a fix for this particular problem as well.
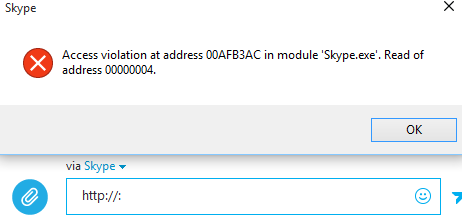
Unlike an earlier bug of a similar nature that crashed the iPhone Messages app, and another that had WhatsApp users in a twist, this particular Skype bug involves no fancy special characters unlike the infamous duo aforementioned. Skype users receiving a message containing “http://:” are pretty much done for as the app will continue to crash as long as that message resides in your chat history. That’s not all, on Windows, sending this message can also crash the app on the sender’s end.

Skype for Mac and the Windows 8.1 Metro app remain unaffected by this bug though. Android and iOS on the other hand remain vulnerable and have their own weak points. We know that the Windows version of Skype keeps crashing with that message in the conversation history, but signing in with the same Skype ID on Android or iOS does not seem to disturb the app at all. What does irk the Skype for iOS and Android, is when it receives that particular message, it ends up in a crash loop similar to the Windows version. Interestingly, sending that message from your smartphone doesn’t seem to bother the Skype app on your end.
Luckily, a fix is available for anyone affected by this bug on the said platforms. Apparently, Skype had taken notice of this issue and have released an updated app for all affected platforms, rendering the bug redundant as of now. There remains no need to uninstall Skype and ask your buddy who pranked you to delete that message so you can sign in again.
Simply head over the Skype website – skype.com – to download the latest release of Skype for Windows, or head over to the relevant app store on iOS and Android to update your existing Skype app.
(Source: Skype)
You may also like to check out:
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

