It’s only been a matter of days since Apple issued OS X Yosemite’s latest point release, version 10.10.5, which fixed a number of important security flaws but it looks as there is already additional woe for the Cupertino-based company to consider. On the back of that point release yet another vulnerability within OS X Yosemite has been discovered and made public, this time without actually informing Apple of the issue before allowing the currently unpatched issue to get into the public domain.
Luca Todesco, an Italian teenager who embarks on security research in his spare time, has released intricate and in-depth details of what’s known as a ‘zero-day vulnerability’ within Apple’s OS X 10.9.5 and OS X 10.10.5 platforms, Mavericks and Yosemite. The issue appears to have been resolved, albeit likely inadvertently, by Apple through the currently in-beta OS X El Capitan, but it still presents some serious concern that the vulnerability exists in Apple’s latest public version of Mac OS X.

According to various reports on the subject, the issue that has been identified within OS X relates to how Apple’s platform handles NULL pointers (a pointer that doesn’t point to an object or function) within applications. It’s this handling, or lack thereof, that opens up the platform for malicious individuals to trick users into accepting the running of malicious code that can then bypass any security restrictions that exist within OS X. This type of vulnerability does actually require the user to explicitly allow the malicious code to run, which is something of a saving grace.
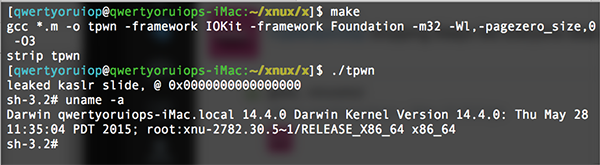
A number of people within the industry have taken exception to how this zero-day vulnerability has been made publicly available. Rather than garner information pertaining to the issue and present it to Apple the researcher has chosen to publish information on the vulnerability via GitHub. He has also published a “third-party” fix for the issue and is calling it NULLGuard. Regardless of your stance on whether or not issues such as this should be reported to Apple in the first instance Todesco makes a valid point by likening his information release to the release of a jailbreak.
It took Apple approximately one month to release a fix for the recently patched DYLD_PRINT_TO_FILE vulnerability. Hopefully this issue can be fixed sooner than that.
(Source: Twitter)
You may also like to check out:
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

