Google is one of the biggest names in services, and while Apple fancies itself as a service company at times, Google is streets ahead. That doesn’t mean that it gets everything right, though, and security company Imperva has released details of a Google Photos vulnerability that could have allowed users’ location data to become available to others.
Thankfully, the issue is now fixed, but for a time it was definitely there, according to the report. The attack required the use of a browser, with users tricked into visiting a website while they were also logged into Google Photos. It wasn’t a low effort affair, however, so it’s also unlikely that this was ever used.

In my proof of concept, I used the HTML link tag to create multiple cross-origin requests to the Google Photos search endpoint. Using JavaScript, I then measured the amount of time it took for the onload event to trigger. I used this information to calculate the baseline time — in this case, timing a search query that I know will return zero results.
Next, I timed the following query “photos of me from Iceland” and compared the result to the baseline. If the search time took longer than the baseline, I could assume the query returned results and thus infer that the current user visited Iceland… by adding a date to the search query, I could check if the photo was taken in a specific time range. By repeating this process with different time ranges, I could quickly approximate the time of the visit to a specific place or country.
While it is obviously good news that this is no longer an issue, it’s once again a reminder that when everything is online, being 100% safe and secure is something that isn’t easy to achieve.
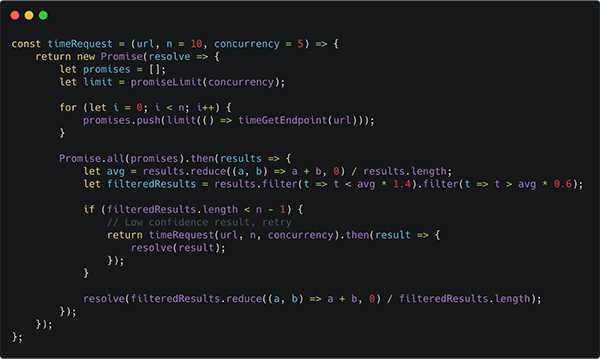
Function used for the aforementioned proof of concept
(Source: Imperva)
You may also like to check out:
- Download iOS 12.2 Beta 6 IPSW Links And OTA Update For iPhone And iPad
- Downgrade iOS 12.1.4 To iOS 12.1.1 Beta 3 For Jailbreak [Guide]
- Jailbreak iOS 12 / 12.1.2 / 12.1.2 Beta 3 With Unc0ver And Install Cydia, Here’s How [Tutorial]
- Jailbreak iOS 12.1.4 Using Luca’s WebKit Exploit May Soon Be Possible
- Download iOS 12.1.4 IPSW Links, OTA Update With Critical FaceTime Bug Patch
- Best Galaxy S10 / S10+ / S10e Case List: Here Are The Must-Haves For Protection
- Galaxy S10 / S10+ / S10e Screen Protector With Tempered Glass: Here Are The Best Ones
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple, and the Web.

