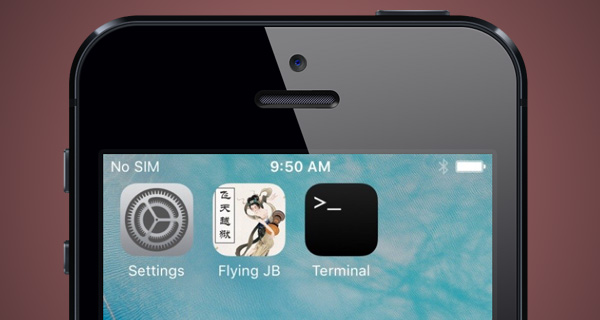
Chinese dev Min Zheng, better known by his Twitter handle @SparkZheng, has demonstrated a new iOS 9.2.1 jailbreak called “Flying JB”. The video demonstration shows the Flying JB app being executed to successfully jailbreak a 32-bit iPhone running iOS 9.2.1. The jailbreak itself is made possible and based entirely on an extremely powerful 15-year old kernel HeapOverFlow vulnerability – inpuTbag – that exists within the particular firmware version that’s being liberated in the video.
The hacker has also publicly asked for credit to be given to Cererdlong and Eakerqiu for their part in making the Flying JB possible for those running a compatible device on a compatible version of Apple’s firmware.
It’s extremely interesting, and potentially exciting for some, to see a functioning jailbreak being demonstrated on iOS 9.2.1, but as you might expect from the modern jailbreak landscape, it does come with certain caveats.
First and foremost, the aforementioned kernel vulnerability has been patched as of iOS 9.3.2 by Apple, meaning that the Flying JB solution simply won’t work on devices running that firmware. Secondly, Apple has also added additional “entitlements” as of iOS 9.3, meaning that it’s a lot harder to perform the jailbreak on iOS 9.3 and iOS 9.3.1.
Additionally, the Flying JB solution is actually only capable of jailbreaking Apple’s 32-bit devices, so that means it only works for phones and tablets that were built before Apple moved across to its 64-bit architecture. That’s essentially an iPhone 5 or lower, and of course, only those capable of running iOS 9.2.1, so the iPhone 5, iPhone 5c and iPhone 4s.
Finally, the Flying JB solution doesn’t actually come with a graphical interface like the majority of popular jailbreak solutions, such as Pangu9, and will therefore more than likely be extremely difficult to use for the average iOS device owner.
If you like nothing more than to tinker, and are prepared to potentially risk the integrity of your device if something goes wrong, then you can download and compile the Flying JB source code by downloading it from the Zheng’s GitHub. It’s important to note that the source available on GitHub isn’t all you’ll need to jailbreak your device as it doesn’t include the sandbox escape.
As always, we will let you know more as and when it progresses.
Till then, check out the hack in action in the video embedded below.
You may also like to check out:
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

