An extremely popular figurehead in the iOS jailbreak community has also confirmed that Apple’s decision to leave the 64-bit kernel cache in iOS 10 beta 1 unencrypted was not an accident.
If you like to keep abreast of what’s going on in the world of iOS, then you may remember that security researchers were shocked to find that iOS 10 beta 1 had an entirely unencrypted kernel. That shock was intensified even further when an Apple publicly confirmed that the lack of obfuscation in the codebase was actually intentional, with the company taking the move to “optimize the operating system’s performance without compromising security”.

Apple may have moved fairly promptly to confirm that the 64-bit kernel was left intentionally unencrypted in iOS 10 beta 1 as part of an effort to improve performance, but for one reason or another, Apple’s public declaration didn’t wash with some individuals involved in the world of mobile security.
In fact, some researchers had suggested that Apple’s official announcement had only been made to try and dilute any security concerns that consumers may have while they worked internally on patching the issue for the release of iOS 10 beta 2. Well, iOS beta 2 is now officially and veteran jailbreaker MuscleNerd has taken to Twitter to confirm that the lack of encryption in beta 1 was not only intentional, but that Apple has taken things a step further with beta 2:
It was no accident. Apple left even more images unencrypted in 10.2b2 (e.g. all ramdisks and 32-bit bootloaders!)
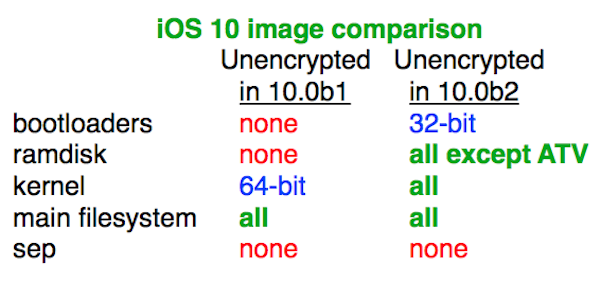
The tweet not only confirmed that the lack of encryption was an intentional act by Apple, but also highlighted the fact that iOS 10 beta 2 has shipped with additional images unencrypted. The accompanying image associated with the tweet shows that the 32-bit bootloader in iOS 10 beta 2 is also now unencrypted, as are all ramdisk instances except for the Apple TV. All kernels and all main filesystems within the iOS 10 beta 2 firmware are also suffering – or benefiting from depending on how you look at it – a distinct lack of any type of encryption.
To the average iPhone, iPad and iPod touch user, this new information pertaining to the lack of encryption will mean absolutely nothing. However, to security researchers involved in the world of jailbreaking, it could potentially mean that Apple has made it a lot easier to find potential kernel exploits that could be leveraged to produce a functioning jailbreak solution going forward.
(source: MuscleNerd [Twitter])
You may also like to check out:
- How To Downgrade iOS 10 Beta To iOS 9.x [Tutorial]
- Jailbreak iOS 9.3.2 / iOS 9.3.3 Status Update [Latest]
- Download iOS 10 Beta 2 & Install On iPhone 6s, 6, Plus, SE, 5s, 5c, 5, iPad, iPod [Tutorial]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

