That untethered jailbreak demo that we posted about last night? Well it looks like the hacker behind the exploit is going to save it until Apple releases iOS 4.3.1.
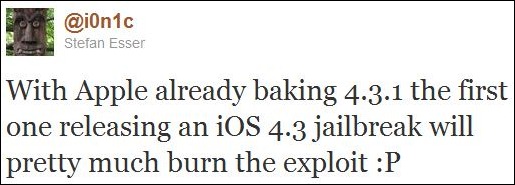
i0n1c: With Apple already baking 4.3.1 the first one releasing an iOS 4.3 jailbreak will pretty much burn the exploit 😛
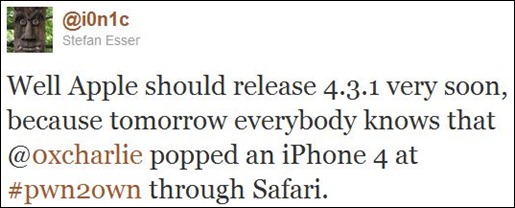
i0n1c: Well Apple should release 4.3.1 very soon, because tomorrow everybody knows that @0xcharlie popped an iPhone 4 at #pwn2own through Safari.
Why you may ask? At Pwn2Own contest, iPhone 4 was hacked via vulnerability which was found in Mobile Safari running iOS 4.2.1. This vulnerability also exists in iOS 4.3 but all devices running the latest version of iOS are safe until hackers find a way to bypass the ASLR (Address Space Layout Randomization) which Apple has implemented for all supported devices starting from iOS 4.3.

In an interview, winners of Pwn2Own told ZDNet that bypassing ASLR security in iOS 4.3 is harder to do then what most think it is.
If you update your iPhone today, the [MobileSafari] vulnerability is still there, but the exploit won’t work. I’d have to bypass DEP and ASLR for this exploit to work.
As of 4.3, because of the new ASLR, it will be much harder.
According to Charlie Miller, the winner of this years’ Pwn2Own contest, Apple has been informed about the vulnerability and they are going to fix it in the next update.
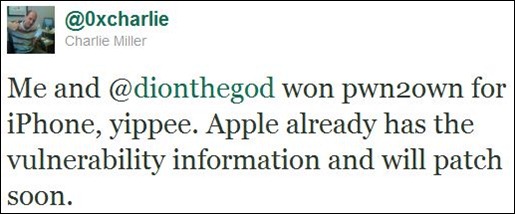
@0xcharlie: Me and @dionthegod won pwn2own for iPhone, yippee. Apple already has the vulnerability information and will patch soon.
So is iOS 4.3.1 release imminent? Not anytime soon I think. Since the exploit mentioned above in iOS 4.3 requires ASLR to be bypassed, I don’t think Apple will be worried too much. Or not until someone figures out a way to bypass ASLR and makes the technique public. What do you think?
You can follow us on Twitter or join our Facebook fanpage to keep yourself updated on all the latest from Microsoft, Google and Apple.

