An app going by the name of Tether makes locking and unlocking your Mac a case of walking away from, or towards your desk. More details can be found right here.
Security is never far from the headlines these days and with very good reason. We entrust so much of our information to our computers and mobile devices that we really shouldn’t be surprised that they are targets for criminals, be they organized or opportunistic.

We spend a lot of time, and sometimes a lot of money on trying to keep our data safe, but we often forget that the most basic of protection can be the most effective form of deterrent. That’s why the use of fingerprint sensing technology in Apple and Samsung smartphones is so important, because before unlocking a device became a case of just touching something, nobody used PIN codes.
The same goes for our computers, and even though they have usernames and passwords as a matter of course these days, we’re willing to bet that few people actually lock their computer when they are away form it. That needs to stop, and Tether makes it easier than ever to lock and unlock a Mac.
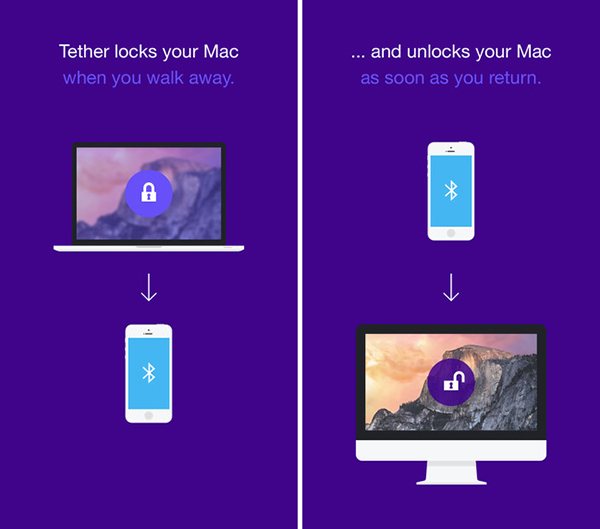
A bundle of two apps – one for the Mac and one for the iPhone, but both free – Tether relies on Bluetooth 4.0’s low energy abilities to track how far away an iPhone is from the Mac it has been configured to work with. Once the two get too far away, the Mac locks. Return the iPhone to the proximity of the Mac and voila, it unlocks. It’s magic Jim, but not as we know it.
Apps like Tether have been around for a while, but this one actually works reliably and, importantly, costs nothing. In fact, the app’s developer didn’t intend to make it in the first place. After using it to as a development platform for other projects, the UK firm behind Tether decided to release it for everyone to use. That explains the lack of a price, too.
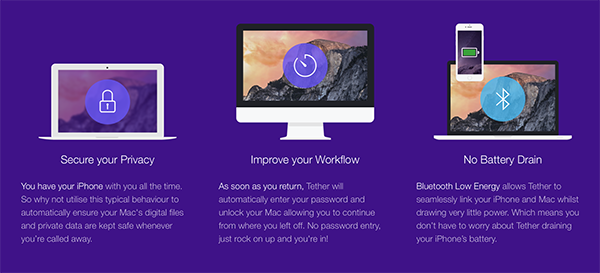
It’s that price that makes Tether so interesting and, importantly, useful. If this makes you lock your computer when you leave it then we’d call that a win in our books. So long as nobody can just walk up to your machine and have instant access to anything, then that’s one avenue of attack thwarted.
Well done you.
You can download Tether for iPhone from here, and the companion Mac app from here.
You may also like to check out:
Be sure to check out our iPhone Apps Gallery and iPad Apps Gallery to explore more apps for your iPhone and iPad.
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

