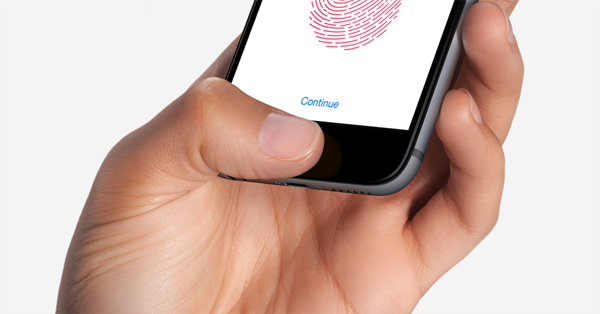
Apple has taken the opportunity to acknowledge that any third-party repair to the Touch ID Home button on the iPhone 6 or 6 Plus can eventually result in the device being bricked when iOS is updated on the device. Rather than being an error and something that has slipped through the net, Apple is confirming that this is indeed a deliberate security feature designed to protect users.
The problem appears to have been affecting a growing number of users who have opted to have some kind of unofficial repair work carried out on the Home/Touch ID button or connecting cable internally. Those affected users have been receiving “error 53” when trying to update the device firmware via iTunes, and as yet have not found a way to actually get the device back up and running.
Kyle Wiens of iFixit has previously shone light on the issue by highlighting that the “error 53” page on his site has been had more than 183,000 hits. That number along provides a fairly decent indication that the problem is being experienced by a far reaching set of users:
The problem occurs if the repairer changes the home button or the cable. Following the software upgrade the phone in effect checks to make sure it is still using the original components, and if it isn’t, it simply locks out the phone.
It all sounded a little difficult to believe, until Apple actually chimed in with an official response that outlines the intended behaviour designed to protect the Secure Enclave within the device:
We protect fingerprint data using a secure enclave, which is uniquely paired to the Touch ID sensor. When iPhone is serviced by an authorised Apple service provider or Apple retail store for changes that affect the touch ID sensor, the pairing is re-validated. This check ensures the device and the iOS features related to touch ID remain secure. Without this unique pairing, a malicious touch ID sensor could be substituted, thereby gaining access to the secure enclave. When iOS detects that the pairing fails, touch ID, including Apple Pay, is disabled so the device remains secure.

The explanation from Apple actually makes perfect sense. There will likely be a heap of affected users who are outraged by the fact that Apple is purposely running checks to determine whether or not it should brick the device, rendering it unusable. However, all it would take is for one security breach related to this type of repair for Apple to find itself in a publicity nightmare relating to security. Whether or not there is a way to bring the device back to life is still up in the air.
(source: The Guardian)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

