When iOS 10.3 was released by Apple, the software brought with it an important bug fix that plugged a security flaw in Safari, which had the potential to allow scammers to extort money out of unsuspecting iPhone owners via a JavaScript pop-up.
An article published by security firm Lookout yesterday outlines the security flaw as well as the potential fallout of it should it have been taken advantage of. Apparently, scammers would target users who visited por*ographic websites, throwing them into an endless loop of pop-ups that, while possible to bypass if you had the know-how, would have the potential of leaving less tech-savvy users in something of a spin.

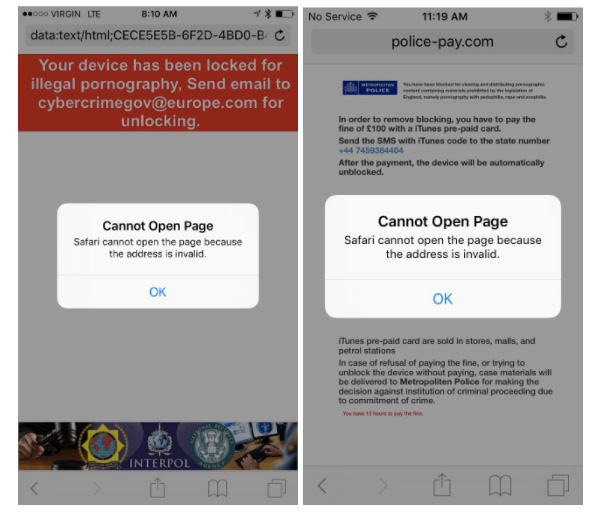
Posting as law enforcement, the scammers would then attempt to extort money from the iPhone users, often in the form of iTunes gift cards (because that’s how law enforcement accepts payments, apparently) before promising to unjam Safari once payment had been made.
While a simple clearing of Safari’s cache would fix the problem on impacted devices, that is only good if you know that is the fix and how to implement it. Most people, it seems, do not.
The scammers abused the handling of pop-ups in Mobile Safari in such a way that a person would be “locked” out from using Safari unless they paid a fee — or knew they could simply clear Safari’s cache (see next section). The attack was contained within the app sandbox of the Safari browser; no exploit code was used in this campaign, unlike an advanced attack like Pegasus that breaks out of the app sandbox to install malware on the device.
The scammers registered domains and launched the attack from the domains they owned, such as police-pay[.]com, which the attackers apparently named with the intent of scaring users looking for certain types of material on the Internet into paying money.
If you have not yet updated to iOS 10.3, we suggest you do it soon, provided you don’t care about jailbreaks, of course.
(Source: Lookout)
You might also like to check out:
- How To Downgrade iOS 10.3 On iPhone Or iPad
- Download iOS 10.3 Final IPSW Links For iPhone And iPad
- Jailbreak iOS 10.3 / 10.2.1 For iPhone And iPad [Latest Status Update]
- iOS 10.3.2 Beta 1 Changes / Release Notes: What Are The New Features?
- Download: iOS 10.3.2 Beta 1, macOS 10.12.5 Beta 1, watchOS 3.2.2 Beta 1, tvOS 10.2.1 Beta 1 Out Now
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

