If you thought those little bugs in OS X Yosemite were all you had to deal with, wait till you check out this next one. According to tests conducted on the latest version of Apple’s OS X platform, Yosemite carries a privacy glitch in the Spotlight search feature, releasing some very sensitive data to spammers, phishers, and online tracking companies. What information are we talking about here and how is this happening? Head on after the jump for further details.
This vulnerability was first reveled a while back, but further tests were needed to prove if the bug was real or not, and guess what? It is, and it’s quite alarming.

Apparently, if you’re using Apple’s Mail app and are a frequent user of it, you should be nervous right about now. Why? See, not only does this glitch reveal your system’s IP address to spammers and the like, but your details such as bank info, accounts, and an array of other personal info is right up there for the grabs if an opportunist hacker decides to exploit this vulnerability.
According to the folks who tested this glitch, the Spotlight feature indexes all the emails received from the Mail app, and when searching on a Mac, the email previews are displayed with external images being automatically loaded. Even with the Spotlight preview for remote content in messages turned off in the Mail app, such content will be loaded, and the same holds true for emails sent to the Junk folder of the Mail app.
Automatic external content load is a huge risk, with spammers gaining the chance to feast on information from the target machine with the use of ‘tracking pixels’ to gather data including, but not limited to, details about the browser being used, the version of Quick Look – a document previewing app – and more.
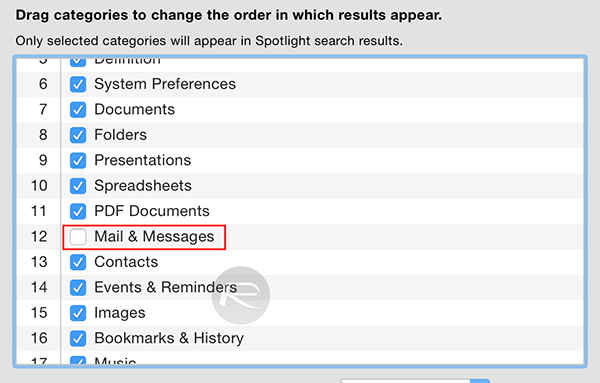
For now, users can avoid the risk associated with this vulnerability by disabling Spotlight search from including ‘Mail & Messages’ via the System Preferences, so that emails are not returned in the search results. This makes sure no external content is loaded as a consequence. Definitely not a fix by any standard, but until Apple decides to address this vulnerability, this is the best option you have.
(via: Heise.de [Google Translate])
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

