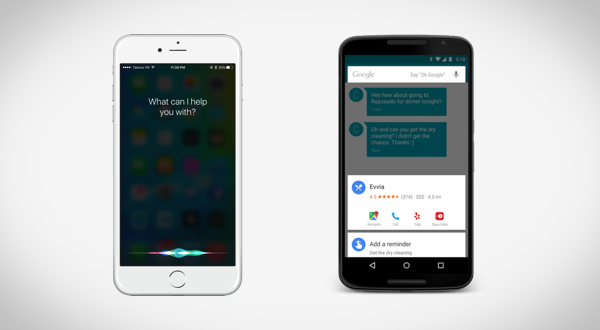
It seems that a day or two can’t go by at the moment without another security researcher or research company finding vulnerabilities in the world’s leading mobile platforms. Two security researchers who have been undertaking work on behalf of the French government have discovered a new clever way for hackers to gain control of an iOS or Android device by tapping into the platform’s digital assistants, Siri and Google Now.
It’s worth noting that this method of gaining access to the iOS or Android device is seemingly a lot more sophisticated than simply tricking the user into downloading a third-party application that has been infected with malware or adware. This latest method of gaining access to the device relies on the attacker to be using the wire inside of a set of headphones to send electromagnetic signals via GNU Radio software directly from a laptop to the targeted mobile device. This method of access, which occurs from more than 16 feet away, then allows commands to be sent to the mobile devices, and consequently allowing the attackers to tap into Siri or Google Now.
The level of commands that could be issued to Siri or Now via this means of access is currently unknown, but there’s no arguing that hackers could instruct Siri or Google Now to create and send text messages, invoke a phone call directly from the phone, or even visit a malicious website via the Mobile Safari or Chrome browsers. All of these methods of access could result in the user’s device unknowingly telephoning a premium rate number or visiting a website designed to run malicious code remotely for extracting sensitive information.
One of the saving graces of this particular “hack” is that the iOS or Android devices in question are only actually susceptible to the attack when a set of headphones are connected to it. Those connected headphones must also be microphone enabled in order for the command to be given. The necessary criteria that needs to be met in order for the device to actually be hacked really narrows down the chances of it happening. There’s also the fact that any provided command via GNU Radio means, that targeted devices would still show the Siri or Google Now interface alerting the user.

It’s unlikely that this mechanism of access will be taken advantage of on a large scale, but nevertheless it’s still extremely interesting and definitely worth reading up on. The researchers in question have presented their findings during a security conference and published a white paper on the topic for those who wish to learn more. You can access this white paper here.
(Via: WIRED)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

