Apple today released iOS 9.3.5 for iPhone and iPad, with the update available for free to anyone who owns a device that is capable of running iOS 9 and above. The update brings with it three important security fixes that, at this stage, are deemed vital for all users, unless they want to jailbreak, that is. More on that in a minute.
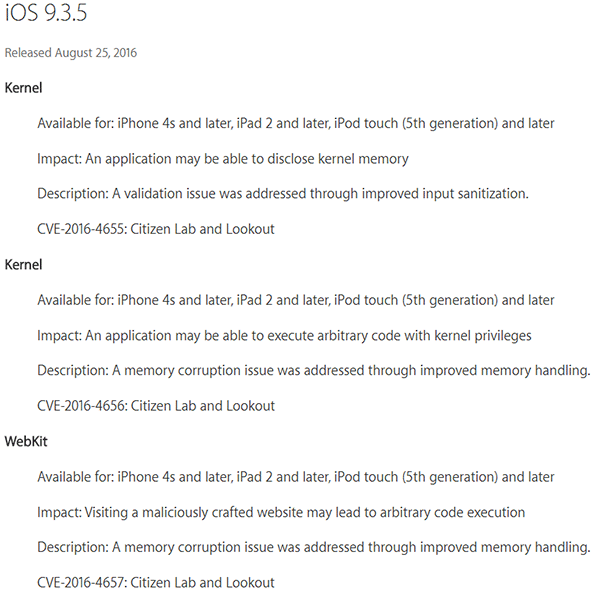
Having already been patched as part of last Friday’s iOS 10 beta 7 but now also available as an iOS 9 update for those not on Apple’s developer or public beta release programs, the three security risks were of a significant nature and potentially allowed malicious access of a user’s device via the execution of arbitrary code. All three issues and their fixes were detailed by Apple in the iOS 9.3.5 security document, available on Apple’s website.

The patch comes after a UAE human rights defender received a malicious-looking link in a text message on his iPhone, which he shared with Citizen Lab and Lookout Security. The security research firms found the link capable of remotely jailbreaking a target device, tracking it, and even taking control of its microphone. It has been noted that the attack, which was tracked back to Israeli spyware company NSO group, employs an exploit very much along the lines of the solution for which Zerodium offered a million-dollar bounty last year. The vulnerabilities involved in use by the attack were then reported directly to Apple, and here we are.
Right now, the obvious advice is to update any and all compatible iOS devices in your possession in order to ensure the above fixes are implemented.
As a byproduct of these fixes, though, it’s important to note that iOS 9.3.5 is not able to be jailbroken at this time, meaning those who do like to keep their jailbroken status would be better sitting tight and waiting for a patch to potentially be made available via Cydia which patches these vulnerabilities on jailbroken devices. In the meantime, we suggest avoiding tapping any links that don’t go somewhere you know is legitimate.

Below are the three fixes, as detailed by Apple in the aforementioned security document:
You may also like to check out:
- Jailbreak iOS 9.3.5 / iOS 9.3.4 For iPhone And iPad [Status Update]
- Download iOS 9.3.5 IPSW For iPhone, iPad, iPod touch [Direct Links]
- Want To Downgrade iOS 9.3.5 On iPhone, iPad, iPod touch? Here’s What You Need To Know
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

