Here’s how the iOS 9.3.5 Phoenix jailbreak works on compatible 32-bit iPhone, iPad and iPod touch devices. Details here.
It feels like there has been a long period of inactivity in the world of jailbreaking, which is why it was exciting to see the recently released iOS 9.3.5 Phoenix jailbreak tool turning some heads. Jonathan Levin, the author of a number of publications relating to macOS, iOS, and Android, has taken the opportunity to capitalize on that reason by posting a write-up explaining exactly how the 32-bit Phoenix offering works.

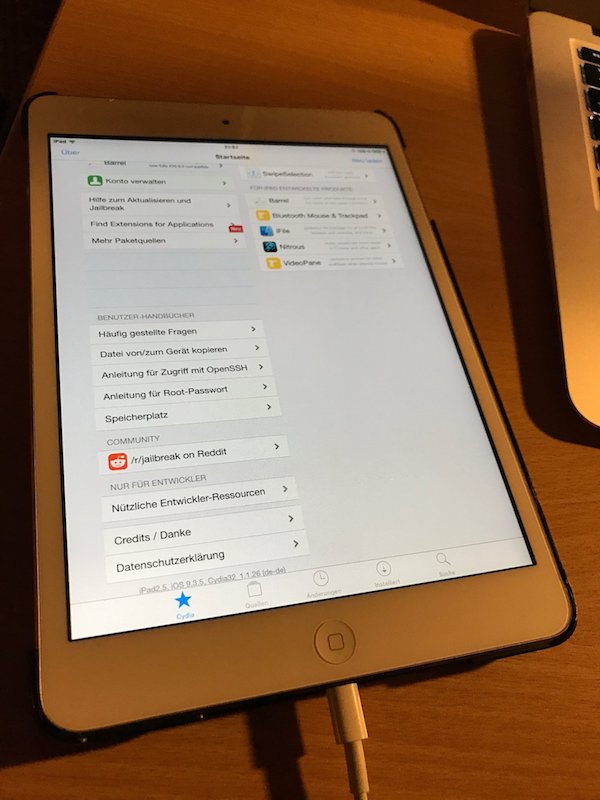
Most owners of a 32-bit device running iOS 9.3.5 will not really have much interest in how the jailbreak functions and goes about its business, or even how the Phoenix solution came into existence thanks to the underlying vulnerabilities which have been exploited during its creation. Instead, most of those device owners will likely simply want to ensure that they get it installed onto their device quickly so that they can start enjoying the benefits that it brings, such as immediate access to Cydia and all of the tweaks within.
However, those with a keen interest in mobile security research, or have a long-standing place in the jailbreak community and are interested in how these tools actually get to a public distribution stage, the write-up by Levin will actually be extremely interesting and will likely expose some information which was previously unknown. One thing that device owners may not know is that the history of the Phoenix jailbreak can be traced back to an extremely polarizing security researcher named Stefan Esser:
The initiative to the jailbreak can be traced to Stefan Esser, who boasted of its ease and even raised a Kickstarter campaign for an online training course with a goal of 111,111 Euro. One of the promised deliverables was such a jailbreak, contingent on the “all-or-nothing” nature of crowdsourcing.
The document from Levin starts off quite light in the fact that it gives a brief history of the jailbreak, including the fact that a number of prominent figureheads took over the process after Esser decided not to deliver based on the failed Kickstarter campaign. It then jumps into a very technical overview of how the tool works, including how it exploits specific vulnerabilities, with Levin describing part of the process as “embarrassing and straightforward to exploit.”
If you are planning on using Phoenix to jailbreak your iOS 9.3.5 32-bit device, or have an interest in security research, then you can view the full write-up here.
You may also like to check out:
- Download Kodi 17.4 RC1 APK For Android And Mac Devices
- iOS 9.3.5 Jailbreak Untethered Allegedly Done And Coming Soon?
- Download Kodi 17.3 On Raspberry Pi 3, 2, 1 Or Zero, Here’s How
- Downgrade From iOS 10.3.3 To iOS 10.3.2 No Longer Possible With iTunes, Here’s Why
- Download iOS 11 Beta 5 IPSW For Your iPhone, iPad, iPod touch [Dev Release]
- Jailbreak iOS 10.3.3 / 10.3.2 / 10.3.1 / 10.3 For iPhone And iPad [Latest Status Update]
- Download iOS 11 Beta 5 & Install On iPhone 7, 7 Plus, 6s, 6, SE, 5s, iPad, iPod [Tutorial]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

