Say what you like about Microsoft Windows and its fairly obvious shortcomings and issues, but you can’t deny that Microsoft has found a seriously regular rhythm when it comes to pushing out security updates and critical fixes to the operating system. The unofficial term “Patch Tuesday” is a reflection of that hard work and dedication, referring to the weekly regularity of Microsoft’s updates. However, when those updates start to filter through on a Monday, which is what happened, you know its time to take things seriously. You may want to get to that Windows update mechanism right now if you haven’t already.

The recently released security update labelled MS15-078 (KB3079904), which was deemed critical enough to be made public before the regular schedule, is available for all releases of Windows since Windows Vista and fixes a fairly critical vulnerability that could allow for exploitation of the Microsoft Font Driver to allow remotely stored code to be executed without the users knowledge. Microsoft is deeming the security update as “critical” and lists the affected software directly within the Microsoft Security Bulletin that applies to this update:
This security update resolves a vulnerability in Microsoft Windows. The vulnerability could allow remote code execution if a user opens a specially crafted document or visits an untrusted webpage that contains embedded OpenType fonts.
So, in terms of the layman, if you happen to visit a website or open a purposely sent document that uses a custom font, then it could be entirely possible for a malicious individual to exploit that bug within the font drivers to execute malicious code directly on your machine. There really isn’t a limitation to what the executed code could be designed to do. It could as sinister as invoking the webcam on the machine to capture images or even extract and upload sensitive data directly to remote servers over the Internet.
The fact that Microsoft has labelled this bug as “critical”, it’s highest security rating, and pushed it out ahead of its usual update release process should probably tell its own story. So if you are running a version of Windows listed in the Microsoft Security Bulletin MS15-078 here then you best get yourself over to Windows Update and fix that vulnerability post haste.
Launch Windows Update, click on ‘Check for updates,’ and then download and install security update KB3079904 for your version of Windows, as shows in the screenshot below.
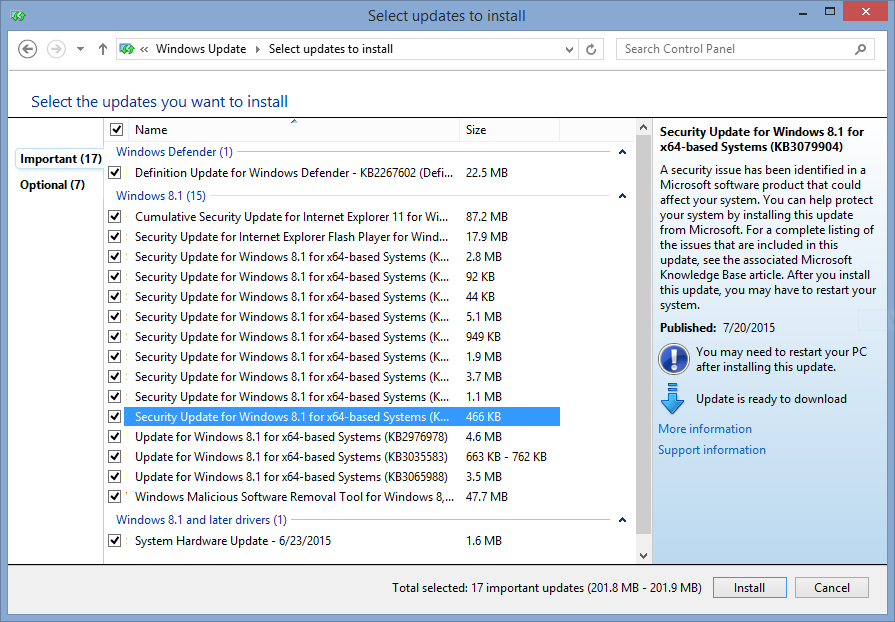
(source: Microsoft)
You may also like to check out:
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

