The passcode lock is a key security measure protecting the personal and security-related data of iPhone, iPad and iPod touch users far and wide. But recently, it emerged that a hardware-based hack in the form of a little black box could bypass this measure on iOS 8.1 and below, including non-jailbroken devices, using a brute-force tactic, and following on from that, one developer has created a software based utility now that can do likewise without the need for additional hardware, but it works on jailbroken devices only.
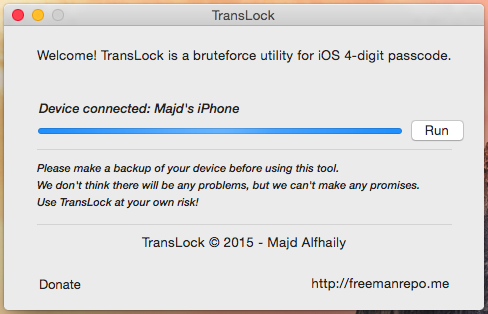
After the black box attack revealed last week, which essentially bypasses the limit on passcode retries, Majd Alfhaily has come up with TransLock, a tool that uses the same tactic but is purely software-based. Since a jailbreak offers very few limits on what kinds of code can be executed, TransLock overrides the retry limit, and can punch in a new passcode attempt every five seconds.

At such speed, it could successfully break into a passcode-locked device within 14 hours, and since it appears to try out passcodes sequentially, those secret codes beginning in the smaller numbers would be cracked much more quickly.
It’s quite staggering that, despite the widespread hacking and leaking of personal data that occurs on a frequent basis, many are still pretty blasé about security. Using a password or passcode related to, say, your name or date of birth is not an ideal countermeasure against being hacked, and depending on what kind of data you have stored on your device, you could have your banking details stolen, privacy invaded, and cause a whole lot of hassle that might have been very avoidable.
Suffice to say, using a difficult-to-guess password, rather than a simple one, would be advisable. Since Alfhaily’s hack has the potential to hack compromise any passcode within 14 hours, we’d suggest opting for an alphanumeric password including numbers, letters and symbols if possible, which will give you a better chance of keeping hackers at bay.
Sure, it’s an inconvenience to have to type in more characters than your simple four-digit combination, but it’s a lot more inconvenient to have your device infiltrated and used for unscrupulous ends.
For those concerned, TransLock is not yet out in the wild, but Alfhaily does intend to roll it out very soon, with libTransLock already available on GitHub.
Again, this only affects jailbroken devices. Non-jailbroken devices are completely safe from it.
Check out the video of TransLock in action, and do let us know what you think in the comments:
(Source: FreemanRepo)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

