A large number of Mac apps are currently at risk of falling foul to a man-in-the-middle attack. The apps, all of which use the Sparkle software update mechanism by which to offer downloadable updates to users, range from the likes of Sketch, VLC and Camtasia all the way up to DxO OpticsPro and uTorrent.
The current situation leaves anyone with an affected Mac app and a habit of connecting to third-party, free WiFi access points potentially at considerable risk.

What’s the issue and how it works?
The issue arises when an application is using an unsafe version of the Sparkle updater software as well as an unencrypted HTTP connection over which to send the data. Those apps which use Sparkle and HTTPS are not affected by this. It’s also worth noting that apps downloaded from the Mac App Store are unaffected because, by their very nature, they don’t need to use Sparkle for app updates.
Sparkle itself has already received an update to plug this particular security loophole, but that’s unfortunately not the end of the story with apps needing to be updated themselves in order to take advantage of it.
A proof-of-concept video has been made, which shows how it is possible for a man-in-the-middle attack to be used to exploit Sparkle’s vulnerability.
As mentioned earlier, while Sparkle has been updated to fix this issue, users will need individual app developers to update their own apps to take advantage of that fact. This isn’t necessarily going to see a quick turnaround, and the alternative option of enabling a secure HTTPS connection over which to send data isn’t always an easy option either. In short, it may be a while before all of the apps (and there are tons and tons of apps that are affected) that use Sparkle and HTTP are safe from this current security issue.
How to find apps on your Mac affected by Sparkle vulnerability:
If you are concerned about whether the apps you use are affected, open a Terminal window and enter the following command to get a list of all apps that use the Sparkle update framework.
find /Applications -name Sparkle.framework | awk -F’/’ ‘{print $3}’ | awk -F’.’ ‘{print $1}’
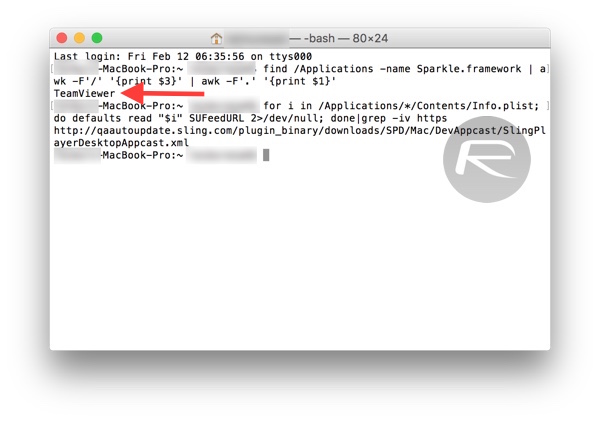
Note that this won’t identify which apps use HTTP instead of HTTPS. For that, the following Terminal command should help.
for i in /Applications/*/Contents/Info.plist; do defaults read “$i” SUFeedURL 2>/dev/null; done|grep -iv https
The command will return URLs that may, in certain cases, point to the developer’s website instead of a domain dedicated to the app itself, so you might have to do some followup searching to identify app names.
The fix?
As mentioned earlier, once you get the list of apps on your Mac that are affected, make sure you head to the developer’s website of all those apps to grab the latest available updates with fix in place for this vulnerability. Currently, this is the only way to make sure your Mac stays safe from Sparkle vulnerability.
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

