A new vulnerability has just been discovered in all Macs that are more than an year old, and the risks associated with it are truly disturbing if an individual manages to exploit it. Apparently, a hacker could take permanent control of the machine, where formatting and reinstalling OS X would not make a difference either.
Pedro Vilaca is a well-known OS X security researcher, and he says that all Macs that were shipped earlier than Q3 of 2014 remain vulnerable, and are the ones that can go into sleep mode. As pointed out by ArsTechnica, Vilaca “found a way to reflash a Mac’s BIOS using functionality contained in userland, which is the part of an operating system where installed applications and drivers are executed.” According to Vilaca, attackers can easily exploit vulnerabilities that are regularly found in Safari and other Web browsers to install malicious firmware which “survives hard drive reformatting and reinstallation of the operating system.”

Last year we saw how the Thunderstrike exploit could install permanent backdoors onto a Mac if anyone could briefly access a machine. A hugely concerning exploit, it was believed that factoring in the need to physically access a Mac meant that the risk would not be spread on a large scale. However, this newly discovered vulnerability allows for an attacker to do all of that, but the key difference is that it can be done remotely and proximity is not an issue here.
Vilaca says that for all this to work, the machine has to be in suspended or sleep mode, and while there’s nothing much users can do at this point to prevent an attack, disabling sleep mode will be a good idea to start with. “The only requirement is that a suspended happened [sic] in the current session. I haven’t researched but you could probably force the suspend and trigger this, all remotely. That’s pretty epic ownage ;-).”
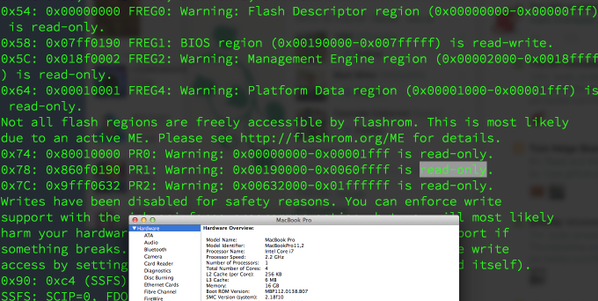
As for how serious can this issue be for the average consumer, it is believed that like the Thunderstrike, attacks using this exploit will be very limited and aimed at very high-value targets, those that the attackers know about and have a high interest in. Meanwhile, the exploit has been tested to work on “MacBook Pro Retina, a MacBook Pro 8,2, and a MacBook Air, all running latest EFI firmware available. And every single one is vulnerable.”
(via: ArsTechnica)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

