The hackers behind recent cyber-attacks on Sony, Nintendo and CIA have struck again! This time, they targeted Arizona Department of Public Safety and were highly successful in their attempt.
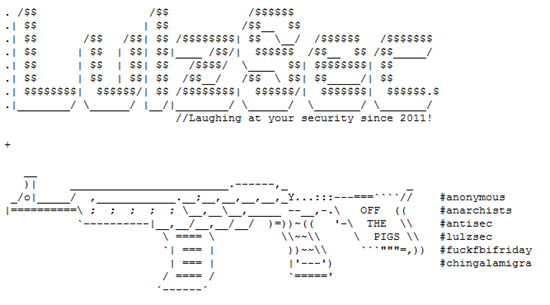
LulzSec posted a bulletin on their website yesterday stating that they are releasing hundreds of intelligence data, personal email correspondence, names along with phone numbers, addresses and passwords belonging to the law enforcers of Arizona:
We are releasing hundreds of private intelligence bulletins, training manuals,
personal email correspondence, names, phone numbers, addresses and passwords
belonging to Arizona law enforcement.The documents classified as “law enforcement sensitive”, “not for public distribution”, and “for official use only” are primarily related to border patrol and counter-terrorism operations and describe the use of informants to infiltrate various gangs, cartels, motorcycle clubs, Nazi groups, and protest movements.
LulzSec says they targeted AZDPS because they are against SB1070.
SB1070 is a legislative act that was passed in Arizona state which is considered to be the strictest anti-illegal immigration law in recent history. Its basic provision is that all “aliens” (persons in a country who are not a citizen of that country) 14 or older who are in the US for more than 30 days must register with the government and must carry registration documents at all times.
LulzSec plans to release more confidential data every week:
Every week we plan on releasing more classified documents and embarassing
personal details of military and law enforcement in an effort not just to reveal
their racist and corrupt nature but to purposefully sabotage their efforts to
terrorize communities fighting an unjust “war on drugs”.

(credit: Louis Abate)
Among the posted data, one document titled “iPhone apps used against officers” is of special interest to us. Within the document are several apps that AZDPS officers must know about when dealing with potential offenders:
- Cop Recorder: App that can be activated while in pocket to record conversation with an officer.
- Trapster (pictured above): A crowd sourced app wherein users can mark places on a map where they believe speed traps have been set up. Other users passing through this area are then alerted.
- Find My iPhone: Officers are told that these apps allow remote deletion of data on the iPhone. So, once they seize a person’s iPhone, it must be shielded from wireless signals so that important evidence may not be wiped out.
The AZDPS’ website is now back up with a statement confirming that the data released by LulzSec is, in fact, the real deal:
The week of June 20, 2011, the Arizona Department of Public Safety became aware that their email system had been compromised by a known cyber terrorism group, known as LulzSec. The group appears to have gained access to the email accounts of at least seven DPS employees. The cyber terrorism group has posted the stolen information on their website.Law Enforcement agencies are working to identify the source of the cyber-attack and have initiated a joint criminal investigation.
A very much positive result from the cyber-attacks is that the victims now go to extra lengths to secure their website and confidential data. But the legality of the cyber attacks are questionable…
What are your thoughts on this, folks? Is LulzSec right in hacking unsecured websites/databases of high profile companies and institutions to expose their “racist and corrupt nature”?
(via AppAdvice)
You can follow us on Twitter or join our Facebook fanpage to keep yourself updated on all the latest from Microsoft, Google and Apple.

