A new strain of malicious mobile adware has yet again been discovered, and it seems to have the potential to cause some serious damage to any device that it sinks its teeth into. It seems that rarely a day or two can pass by at the minute without us hearing about a new form of infection on one of the world’s most popular mobile operating system. Some are extremely malicious and can do serious damage, some are less so. This newly discovered strain, dubbed Kemoge, falls under the former category due to its ability to gain full access to the infected device.
FireEye, the discoverers of the adware,, has named the new strain of adware Kemoge due to the command and control server that it communicates with once it has gone about its business (aps.kemoge.net). Unlike less intrusive and dangerous adware, Kemoge is actually quite frightening in what it can achieve. The newly discovered infection has the ability to actually provide and grant itself full root access to vulnerable Android devices, effectively giving those behind the attack an open door into whatever secrets and information are contained on the hardware.

Like a lot of malicious adware and malware, Kemoge starts out its journey in a seemingly innocent way. Relatively innocent looking applications that are infected by the Kemoge virus are offered to users through third-party application stores, as well as via displayed ads that are capable of installing applications when tapped on. Google provides fairly comprehensive protection and app scanning mechanisms via the Play Store, so by utilizing third-party app stores the individuals behind Kemoge are able to bypass this initial level of detection.
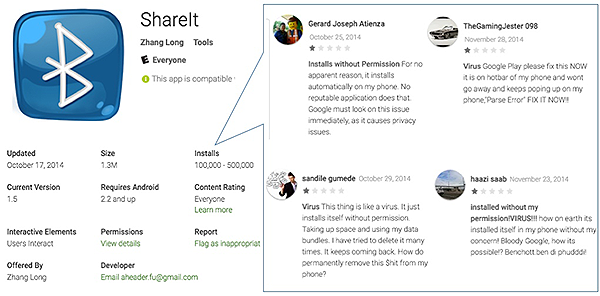
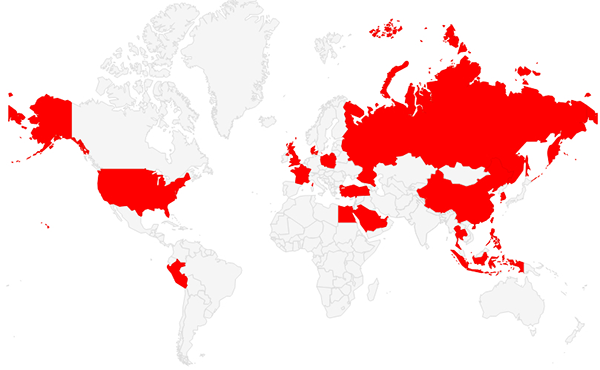
When installed on the device, Kemoge goes immediately to work by aggressively displaying ads at pretty much any point in the Android experience. This could be when apps are running, music playing, or even when just sitting on the home screen. Those ads are bad enough, but there’s also the fact that the adware then attempts to root the device in the background using an array of known security exploits. FireEye’s investigation into the adware shows that it’s currently active in over 20 countries across the world. The company has even traced origins of the infection back to China.
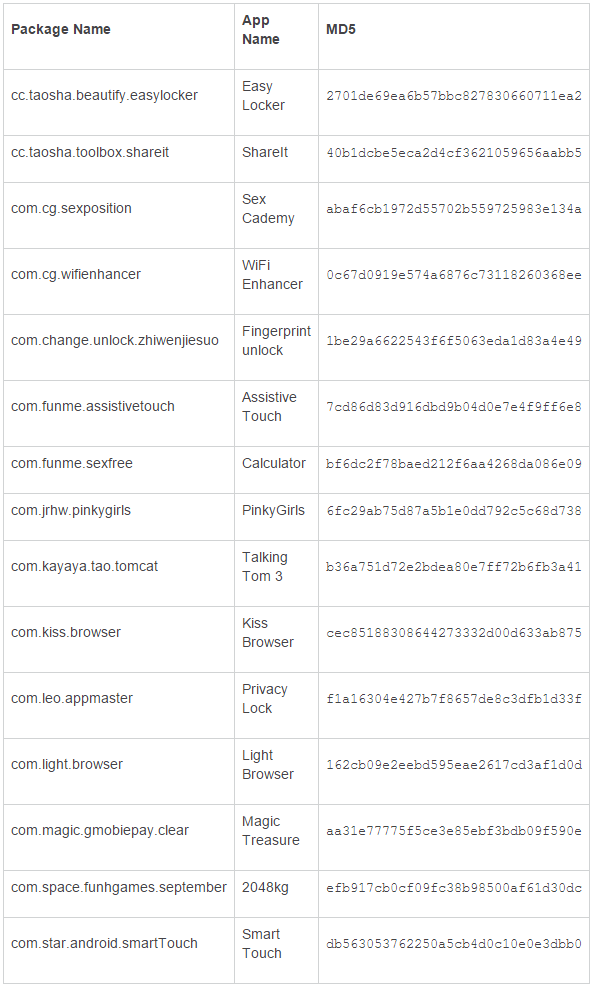
FireEye has also released a list of known apps that are known to be carriers of the Kemoge exploit. Check out the screenshot below for the complete list:
There’s currently no advice on how to remove the infection from the device other than reinstalling the firmware and entirely wiping the phone or tablet. As for the precautionary measures against this exploit, follow the guidelines below:
Never click on suspicious links from emails/SMS/websites/advertisements.
Don’t install apps outside the official app store.
Keep Android devices updated to avoid being rooted by public known bugs. (Upgrading to the latest version of OS will provide some security, but it does not guarantee that you will remain protected.)
(Source: FireEye)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

