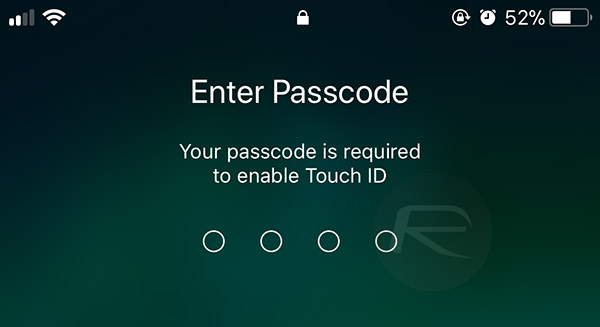
Over the weekend, security researcher Matthew Hickey co-founder of cybersecurity firm Hacker House, reported that a flaw in the way iOS handles pass code input could potentially leave it wide open to brute-force attacks, although that now appears to have not quite been the case as confirmed by the researcher himself as well as Apple.
Originally reported by ZDNet, the researcher claimed that by entering each code from 0000 to 9999 in one string and without spaces, the security mechanisms iOS uses in order to prevent brute force unlocking are bypassed.

An attacker can send all the passcodes in one go by enumerating each code from 0000 to 9999 in one string with no spaces. Because this doesn’t give the software any breaks, the keyboard input routine takes priority over the device’s data-erasing feature, he explained. That means the attack works only after the device is booted up, said Hickey, because there are more routines running.
However, as the same researcher now notes, the testing which suggested all of this may not have actually been accurate. The reason for this is that iOS was treating the entries as a single attempt and thus was not putting its security mechanisms into action. Investigations continue into just what is going on here, but suffice to say, this is not the huge gaping security hole that had initially been suggested.
“I went back to double check all code and testing,” said Hickey in a subsequent message on Sunday. “When I sent codes to the phone, it appears that 20 or more are entered but in reality its only ever sending four or five pins to be checked.”
As you might expect, Apple was somewhat indignant at the suggestion that a flaw in iOS security had been identified.
The recent report about a passcode bypass on iPhone was in error, and a result of incorrect testing
That’s that, then.
Update: Here’s a tweet on this from the researcher himself:
It seems @i0n1c maybe right, the pins don’t always goto the SEP in some instances (due to pocket dialing / overly fast inputs) so although it “looks” like pins are being tested they aren’t always sent and so they don’t count, the devices register less counts than visible @Apple
— Hacker Fantastic (@hackerfantastic) June 23, 2018
(Source: iMore)
You may also like to check out:
- iOS 12 Beta 3 And Public Beta 1 Download, Expected Release Date
- Kodi 18 Leia Alpha 2 APK Download For Android, IPA For iOS, Xbox One, Windows And Mac Released
- Download: iOS 12 Beta 2 IPSW Links, OTA Update Released
- 100+ iOS 12 Hidden Features For iPhone And iPad [Running List]
- Download iOS 12 Beta 2 Configuration Profile File Without Developer Account
- Download iOS 12 Beta 2 IPSW Links & Install On iPhone X, 8, 7, Plus, 6s, 6, SE, 5s, iPad, iPod [Tutorial]
- How To Downgrade iOS 12 Beta To iOS 11.4 [Tutorial]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

