The modern day Internet world faces its biggest challenge right now, and users are affected with it – the data security nightmare. Every now and then, successful hackers manage to break through the security measures of a renowned database, exposing along the way the online identities of hundreds of thousands of users of these services. While the targeted companies manage to recover from these attacks over the course of time, users aren’t always so lucky, where most of them are often left wondering whether their critical info was a part of the leak or not. This is where Australian software architect Troy Hunt’s new project comes in.
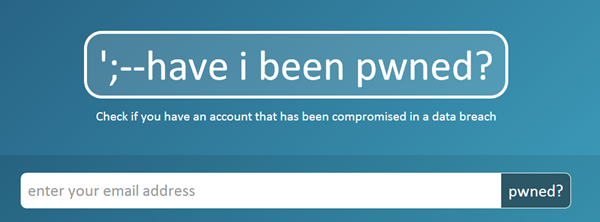
haveibeenpwned.com is a new Web service that allows you to check if your email address was a part of a security leak. As of now, Hunt’s website contains leaked user data from the breaches at Adobe Systems in 2013, the Yahoo! Leak in 2012, Sony’s infamous disaster from 2011, Start for from the same year, and the Gawker security breach in 2010. Hunt plans on adding more data to the list should they happen in the future (something we all wish wouldn’t happen).

To take advantage of the effort being haveibeenpwned.com, all you need to do is feed in your email address at the website, which will then run it against the data from the aforementioned security breaches and let you know if your supplied email address was a part of the list. There are other areas to explore as well, including an FAQs section as well as API support, but the primary functionality revolves around providing a central repository of leaked data and checking supplied email addresses against that. To that extent, the service works perfectly.
This is not the first website of its kind – security researches have come up with similar solutions after any such disaster in the past as well – but Hunt’s project aims at centralizing records to provide assurance against not one particular incident, but all of them, even in the future.
He does go on to discourage breaching a system just to contribute to the project, but something like this is bound to happen in the future as well. Hence, we find this portal useful now and again.
Simply head over to haveibeenpwned.com and get started.
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

