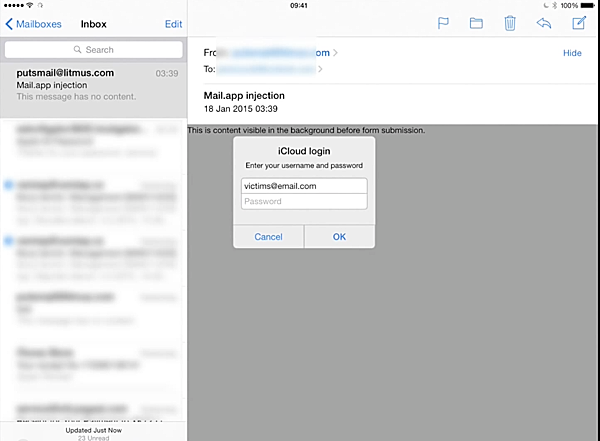
A new bug has been discovered deep within the native iOS Mail app which lets hackers produce official looking iCloud authentication popup that is then presented to the user to steal their login credentials.
Jan Soucek, an email and security specialist with Ernst and Young discovered the bug that takes advantage of a vulnerability within the Mail app that remains unpatched and has the potential to cause a lot of harm to millions of iOS users who regularly interact with incoming emails on an iPhone, iPad or iPod touch.

The bug, which can relatively easily be exploited by malicious minded individuals, is capable of producing extremely official looking iCloud authentication prompts that attempt to engage the user in entering sensitive information. Because the prompts are styled and delivered remotely to look and feel native like Apple’s own it stands a good chance of tricking the user into entering their iCloud associated email address and password without giving a second thought to where that information may actually end up.
The official looking iCloud prompts are achieved by exploiting the bug within the Mail app that allows remote HTML content to be loaded when reading an email received on an iOS device. Due to the nature of the bug, the presented box can be styled and themed to fit the exact look and feel of an official Apple iCloud authentication prompt that appears so often throughout iOS.
Soucek, who discovered the bug in January of 2015, claims that Apple did not respond to the discovery when he notified them of its existence shortly after the discovery. It remains unpatched to this day:
Back in January 2015 I stumbled upon a bug in iOS’s mail client, resulting in HTML tag in e-mail messages not being ignored. This bug allows remote HTML content to be loaded, replacing the content of the original e-mail message….It was filed under Radar #19479280 back in January, but the fix was not delivered in any of the iOS updates following 8.1.2.
Due to the way in which the password “collection” notification is presented via remote HTML there is little chance of a more sophisticated attack being possible due to JavaScript being disabled within Apple’s UIWebView control. With that said, Soucek is still fairly confident that the bug presents a fairly significant risk as it allows for an extremely functional password collector be built using simple HTML and CSS.
Be careful of these official looking notifications, folks. Until Apple offers an official fix, it’s best to not enter your iCloud password in any such prompt when you are still in Mail app.
(Source: GitHub)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

