Security is vitally important, and it will only become even more important as we start to store more and more of our lives online. Be it banking information or photos of our kids that are kept in the cloud, our data and information is best kept behind secure passwords, with those passwords kept in something like LastPass or 1Password, both of which are highly recommended to a lot of users.
Unfortunately for both LastPass and its customers, it has suffered a data breach which has led the company to ask all of its users to reset their passwords as a precaution.

While at the moment LastPass is confident that the hackers were not able to gain access to any information kept within a user’s account, they did make it away with LastPass account email addresses, password reminders and authentication hashes. While users should change their LastPass master password as soon as possible, now does not appear to be the time to panic just yet.
We are confident that our encryption measures are sufficient to protect the vast majority of users. LastPass strengthens the authentication hash with a random salt and 100,000 rounds of server-side PBKDF2-SHA256, in addition to the rounds performed client-side. This additional strengthening makes it difficult to attack the stolen hashes with any significant speed.
At this point it is important to note that LastPass does not believe that user data, in the form of passwords and usernames for sites stored within it, was accessible at any time. Nevertheless, a reset of your LastPass master password is believed to be the best course of action, and if you happen to use that same password elsewhere, it may be wise to change that password as well. But nobody does that anyway, do they?
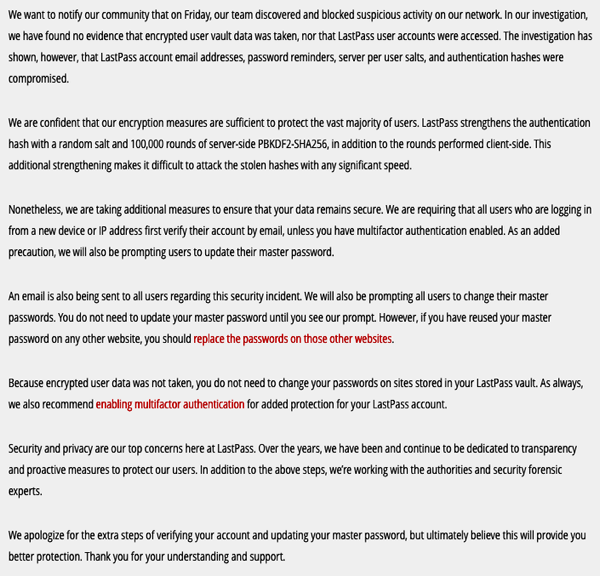
Here’s the complete security notice from LastPass on their very own website:
LastPass is an online service that lets users store credentials for websites and services, meaning they only need to remember one strong master password in order to access all of their accounts. That obviously makes it a prime target for hackers. Luckily, in this case at least, it seems the worst outcome has been avoided and user data is safe.
So there’s that, at least.
(Source: LastPass)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

