It hasn’t been a great week for Apple in terms of security. The Cupertino company is currently coming under heavy fire for a SSL security issue that was recently discovered to be present in both iOS and OS X. The software vulnerability, which is being referred to as the “goto fail” has the potential to provide malicious individuals with the ability to intercept and record data that the user believes to be secure. In addition to the “goto fail” flaw, it is now being reported that an issue has been found in iOS that makes the iPhone and iPad firmware susceptible to stealth key logging activities.
Security researchers from FireEye claim to have discovered the vulnerability within iOS that could potentially allow a less than reputable app to record what the user is doing on an infected device. Keystroke logging – the action of recording the keys struck on a keyboard – has been a big problem in the past for those using desktop computers or notebooks. The act is generally carried out in a covert manner, with the intention of recording data such as usernames, passwords and secure IDs and breaching security, although it does have legitimate research and educational uses.

The newly discovered vulnerability in iOS is said to affect jailbroken and non-jailbroken devices noth, and could potentially allow all keys typed, volume interactions and biometric detections via Touch ID to be logged and recorded without the user’s knowledge. The FireEye blog post states that the issue is known to affect iPhones and iPads running iOS 7.0.4, 7.0.5 and the latest 7.0.6 as well as hardware running legacy versions of Apple’s mobile operating system on 6.1.X. To highlight the flaw, and to show the extent of what is possible, the firm have also created a “proof-of-concept monitoring” app that not only bypasses Apple’s review processes but also logs information using multitasking capabilities.
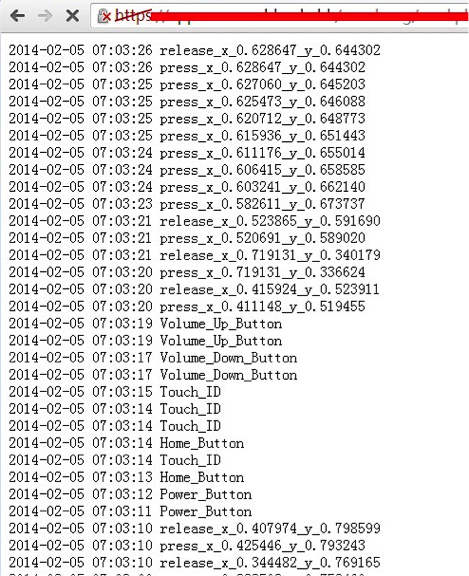
The news of the flaw should provide comfort and alarm for users in equal measures. An original blog post from FireEye – which has subsequently been removed – stated that they had successfully managed to get an app through the App Store review process that exploited this vulnerability. The good news is that the research team behind the discovery is actively working with Apple to provide all necessary details of the flaw with the aim being to get it patched as quick as possible.
(Source: FireEye) (via: ArsTechnica)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

