Wi-Fi networks are literally everywhere. From our homes, to our offices, and heck even in our laundry outlets, we have Wi-Fi networks littered across like a pack of bees going crazy in a flower field. But, while having Wi-Fi around us is all good, but what great does it do when there’s someone hogging all the network’s bandwidth? Don’t you wish you could find that very same guy on the network using a simple app, so you can find a better network for yourself? Of course you can, and it’s as easy as downloading a simple Android app.
The Android app which we’re talking about here is called ‘Wifi Inspector’. Apart from the most obvious name on the planet for an app, it actually has some very cool features which you’ll love.

For starters, it will throw you a list of all the users that are connected to a particular network, giving you a fair idea whether or not the particular Wi-Fi hotspot you’re connected to is congested or not. If you have a long list of connected users, then it’s fairly obvious that you should find yourself a new network to connect to, and if it’s short, then well, you’re golden!
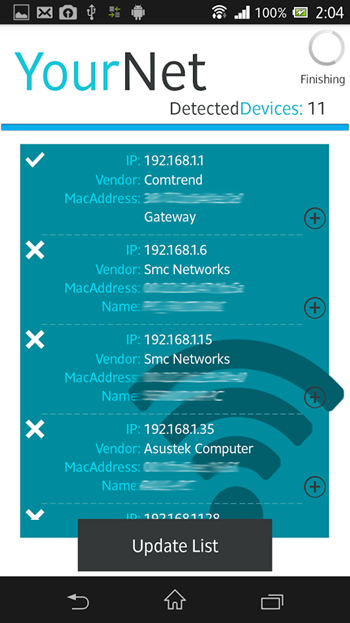
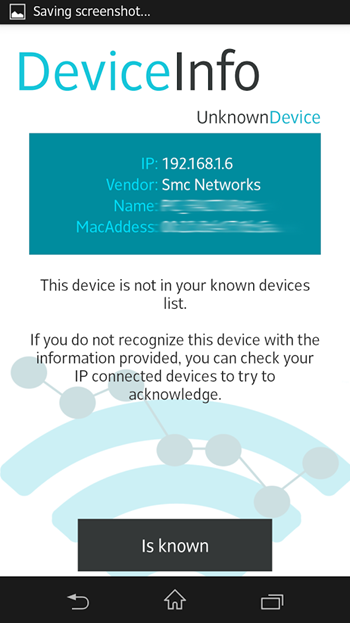
Secondly, Wifi Inspector will let you know if there’s an intruder on your network. This is particularly useful if you’re at home and want to see who is using your Wi-Fi network, and who isn’t, and if you come across someone out of the ordinary (read: Wi-Fi intruder), then you have the chance to take action against them accordingly.
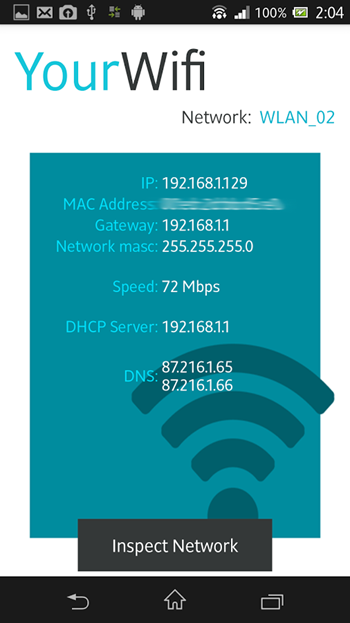
And last but not the least, the app will also show you your IP, MAC address along with the speed you’re getting on a particular Wi-Fi network. Handy information if you’re asking us.
The app does not, in any case, allow the user to kick someone off the network. Its pure function is to analyze the network, and show you a list of users connected to it, and spot someone who shouldn’t belong to that particular hotspot. Nothing more, nothing less.
The app is absolutely free to download, and can be grabbed from the link which we’ve embedded below.
(Download: Wifi Inspector for Android on the Play Store)
Make sure to check out our Android Apps gallery to explore more apps for your Android device.
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

