The open-source nature of Google’s Android is great for those seeking a customizable experience, but in turn, has made the platform an even bigger target for hackers and malware makers. The walled garden of iOS is, without doubt, frustrating at times, but thanks in part to Steve Jobs skepticism (read: hatred) of Adobe Flash, it’s not susceptible to a security flaw threatening four-fifths of the Android community.
As well as being open source, Android is also incredibly fragmented. This means, at any given time, you’re likely to find that the latest release is not necessarily the most widely used, and while Android KitKat is by far the most secure and fluid build to date, it’s also worth noting that at this moment, less than 20 per cent of Droidsters actually use it.

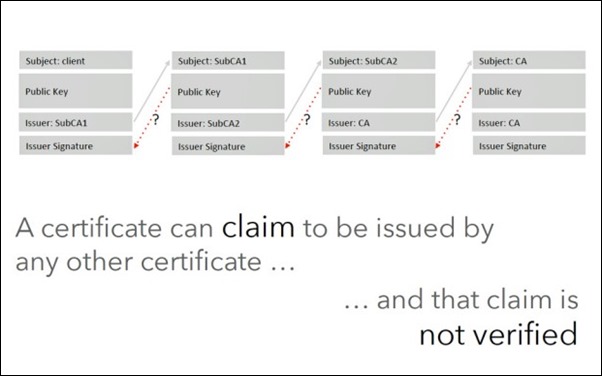
This, in itself, isn’t necessarily problematic, but a ‘Fake ID’ security bug has now been found that allows a malicious app to send faked credentials, disguising itself as a legitimate app. The security firm credited with discovering this new malware feels there’s genuine cause for alarm.
Bluebox Security spotted the inherent flaw in the Android software’s make-up. It affects all Android devices running Android 2.1 and above, including the latest Android KitKat version and Android L preview.
Owners of Android devices running the above mentioned firmwares are left with the threat that a malware app could completely hijack a device by spoofing app permissions, and with these prompts seen as a first line of defense against unscrupulous or otherwise harmful apps, this certainly makes me feel uncomfortable as a frequent Android user.
As per Bluebox’s coverage on the matter, "devices and applications that depend upon the presence of specific signatures to authenticate an application may also be vulnerable [to Fake ID]. As such, any app reliant upon these signature chains are "undermined by this vulnerability."
The good news though is that Google has already released the patch to OEMs and AOSP. The bad news is that we don’t know when will OEMs and carriers implement and start rolling out updates with patch for this serious vulnerability to end users.
What do you make of all this? Be sure to leave your comments via the usual mediums below.
(source: ArsTechnica)
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

