It seems that the iPhone owning and application using world has been going a little bit loopy over the last few days thanks to the revelations that popular journal application Path has been liberating entire address books of data and uploading it to their servers in the form of a plist file without asking for the user’s permission. The company CEO David Morin quickly responded to the outrage by claiming that the name, telephone numbers and email addresses of the user’s address book are captured to help users find friends and family who are using the Path application, but the bottom line is; that the contacts data doesn’t actually belong to the user and therefore they don’t even have permission to upload it should it ever be requested.
In response to this, Path 2.0.6 has been released to the App Store which actually provides an opt-in policy for users, but even the new alert doesn’t exactly make it clear just what the user is opting in to, or out of. While I am pretty sure that story will continue to be in the headlines for a few days before it dies out, infrastructure research and security blog, Peekay, has released some timely information about how users can bypass security measures on an iPhone 4S, 4 and 3GS, making it leak certain information about a user’s address book.

The blog already has security posts about incorrect time settings causing the leak of album images under their belt, but this time their mission was to see if they could peruse the address book and make live video calls from a locked and passcode protected iPhone 4 – and guess what, they could. Using a standard iPhone 4 running a stock version of iOS 5.0.1 (or the iPhone 4S or 3GS), the writers of the blog were able to set up a security passcode requirement through Settings, also ensuring that ‘Voice Dial’ was toggled off meaning the iPhone could not be ordered to place a phone call using the Voice Control function of the iPhone 4.
When pressing and holding the Home button, the Voice Control function is activated – remember, this is an iPhone 4 and therefore does not have Siri capabilities. The blog owners then gave the spoken order to ‘Call Alice‘ with the expected response of ‘Voice dialing is disabled‘ coming back. When sliding to unlock the phone, the standard passcode screen is presented prompting the user to put in their pin code for full device access. By selecting ‘Emergency Calls’ and then activating voice control with a long Home button press, they gave the command once again of ‘Call Alice’ to which the device replied with ‘No Match Found‘.
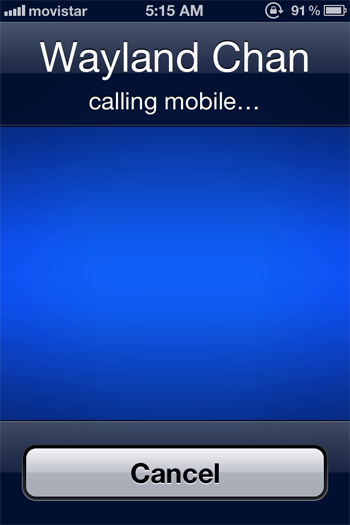
The response of no match found immediately reveals a small amount of information about the address book, confirming that the user does not have a contact stored by that name. Taking the experiment further, when prompted to call a user who does exist in the address book, the locked and passcode protected device obligingly places the phone call to ‘Wayland Chan‘ and by doing so circumvents all security restrictions on the device.
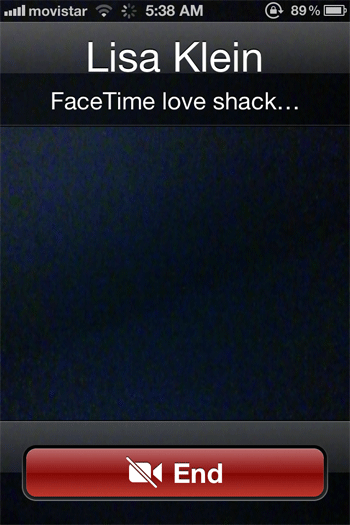
The situation is then expanded when Voice Control is told to call a contact which it exposes has more than one saved number for. By even giving the command of ‘Facetime Lisa Klein‘ the blog owners were able to initiate and complete a fully functioning, live video call from the device which was locked, passcode protected and explicitly had voice dialing disabled.
This certainly seems an opportune time to release such information, especially with the recent Path related fury and definitely gives Apple some issues to address in iOS 5.1.
(via CNet)
You may also like to check out:
- Fix iOS 5.0.1 Contact Bug Issue On iPhone 4S [How-To]
- Apple: Reported iOS 5 iMessage Bug On iPhone Is Not A Bug
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the web.

