As expected, Apple has put its internal engineers to work to issue a quick fix for the recently discovered macOS vulnerability which allows almost any individual to login into a Mac that doesn’t belong to them as a root user.
The vulnerability, which made its way into the public domain on November 29 and was reported to Apple on the same day, essentially meant that anyone with access to the login prompt of a Mac running macOS High Sierra could gain access as a root user without any authentication or password being required.

This particular issue immediately gained traction through social media after the official Apple Support Twitter account was copied into a tweet confirming that the problem exists. Of course, the community immediately jumped on the problem, taking the opportunity to confirm that the problem was evident on various versions of macOS High Sierra and that it did indeed allow root access to be granted to any individual with access to the machine simply by using “root” as the username, leaving the password field empty, and repeatedly tapping the login button.
The official Apple Support Twitter account acknowledged the issue and asked for more information through a direct message but the company has also acted internally to not only find and confirm the problem but to also issue a quick-fire fix for it now.
The fix, dubbed as Security Update 2017-001, means that the rather serious security vulnerability has now been removed and that anyone logging in as root and leaving the password field empty will no longer be able to take control of the machine through the initial macOS login prompt.
Of course, Apple is unlikely to be given the credit it deserves for fixing this issue as a matter of importance within matter of hours, with macOS users instead opting to lambast the company for the fact that the problem existed in the first place.
Apple should not only be given credit for fixing this problem as quickly as it could but for also acknowledging the issue and releasing a statement to let Mac owners know how they could mitigate the problem until a full and final resolution was released. The lessons learned from this episode should be that Apple’s software does indeed ship with bugs, some of which can be serious in nature, and that if serious vulnerabilities are discovered they should be reported to Apple privately instead of being made public.
Available for: macOS High Sierra 10.13.1
Not impacted: macOS Sierra 10.12.6 and earlier
Impact: An attacker may be able to bypass administrator authentication without supplying the administrator’s password
Description: A logic error existed in the validation of credentials. This was addressed with improved credential validation.
CVE-2017-13872
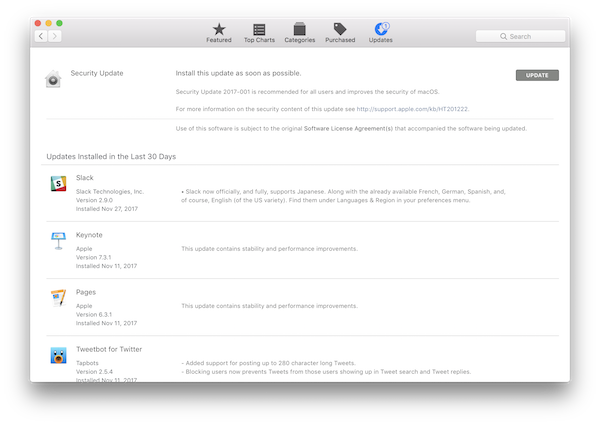
The macOS High Sierra Security Update 2017-001 is available to download right now from the Mac App Store and is HIGHLY recommended update for all Mac users running any version of High Sierra.
You may also like to check out:
- iOS 11.2 Beta 5 Changes, Release Notes And Changelog Details You Need To Know About
- Download iOS 11.2 Beta 5 IPSW Links, OTA For Testing On Compatible iPhone Or iPad
- CyrusVIP Installer Download On iOS 11 Promises No Revokes For Apps And Tweaks On Non-Jailbroken Devices
- vShare iOS 11 Download For IPA Files [No Jailbreak Required]
- Download iOS 11.1.2 IPSW Links And OTA Update For iPhone, iPad, iPod touch
- Downgrade iOS 11 / 11.1.2 On iPhone Or iPad [How-To Guide]
- Jailbreak iOS 11 / 11.1.2 / 11.1.1 On iPhone And iPad [Status Update]
You can follow us on Twitter, add us to your circle on Google+ or like our Facebook page to keep yourself updated on all the latest from Microsoft, Google, Apple and the Web.

